What Is Zero Trust Hardware Access and Why It Matters
Zero Trust’s core principle, “Never Trust, Always Verify”, was created to eliminate implicit trust across users, applications, and networks. However, in most environments, device identity is still assumed, relying on identifiers that can be spoofed or misrepresented.
Zero Trust Hardware Access (ZTHA) extends Zero Trust to its very foundation: the hardware that forms the network and every physical asset connected to it. Zero Trust Hardware Access mandates that a device must be verified for what it truly is before it is trusted to connect, communicate, or operate within the environment.
Sepio’s mission is to enable a Zero Trust strategy that ensures the organization’s foundation – its network hardware and all connected physical devices, is unquestionably trustworthy.
Why Now: The case for Zero Trust Hardware Access (ZTHA)
There’s no better time to anchor Zero Trust in hardware.
- AI is accelerating the discovery of vulnerabilities and lowering the barrier to exploitation.
- At the same time, point solutions continue to fail, fragmented tools create blind spots across IT, OT, and IoT environments, allowing exposure to grow unnoticed.
- Hardware blind spots, including shadow IT, dormant implants, and non-obvious rogue devices – persist because many controls focus on traffic, scanning, or assumptions rather than on actual device presence and identity.
The result is simple: increasing complexity creates more opportunities for adversaries, and therefore greater risk.
The Hardware Gap in Zero Trust
Most security stacks verify users and applications effectively – but they still inherit one critical assumption: a device is trusted simply because it appears legitimate. This leaves blind spots for Shadow IT, spoofed assets, dormant implants, and dual‑use devices that can easily slip past traditional controls.
While enterprises still need traditional security solutions for tactical response, Zero Trust (ZT) provides a strategic framework that shifts security from reactive to proactive. By combining both approaches, organizations can strengthen their overall cybersecurity posture.
Zero Trust eliminates the concept of implicit trust within the network architecture, creating more opportunities to identify threats early and act before an attack succeeds. Critically, Zero Trust extends protection beyond traditional perimeters – an essential capability as telework, Bring Your Own Device (BYOD), and Internet of Things (IoT) devices continue to expand the attack surface.
Zero Trust ensures that access is granted based on who, what, when, where, and how – but answering those questions requires complete device visibility.
Zero Trust Three Guiding Principles
1. Never Trust, Always Verify
Traditionally, internal users and devices are assumed to be trustworthy simply because they exist within the network boundary. But both user identities and device identities can be spoofed, and unmanaged or remote assets fall outside the organization’s control – yet are often treated as “internal.” Zero Trust removes the trust component altogether: every user, device, and workload is treated as untrusted, every time.
2. Verify Explicitly
Access is granted based on dynamic, continuously evaluated policy. Authentication and authorization rely on multiple signals – including identity, location, device health, data sensitivity, behavior, and more. Verification should continue throughout the entire session to maintain strong, adaptive protection.
3. Assume Breach
Under the Zero Trust (ZT) model, defenses operate on the assumption that a breach has already occurred. As a result, devices and users are denied access by default, and resource access is granted only when explicitly validated.
How access is restricted depends on the Zero Trust Architecture (ZTA) an organization adopts:
- Identity‑based architectures require that every user, device, data flow, and access request be thoroughly examined. Access rights are minimized and monitored according to the principle of least privilege, ensuring users receive only the minimal permissions necessary to perform their tasks.
- Micro‑segmentation further reduces risk by limiting lateral movement. Workloads are isolated into small, granular segments, each requiring separate authorization. By dividing the network into multiple “mini‑environments,” micro‑segmentation ensures that even if a threat actor gains initial access, they cannot easily reach their intended target.
A strong Zero Trust Access combines elements from multiple approaches to reinforce the Assume Breach principle. Finally, all configuration changes, access attempts, and network traffic should be logged, inspected, and continuously monitored to detect suspicious behavior early and contain potential attacks.

The Zero Trust Hardware Access Framework
Zero Trust Hardware Access (ZTHA) extends the core Zero Trust principle – “never trust, always verify” – down to the physical layer. In modern environments, hardware is no longer a passive foundation. It has become an active attack surface spanning IT, IoT, OT, peripherals, and “invisible” devices that easily evade network‑centric tooling. Zero Trust Hardware Access offers a structured approach to progress from simply knowing what is connected, to proving what each device truly is, to ensuring continued compliance, and ultimately to enforcing policy in real time when deviations occur.
This framework is organized into five layers, moving from foundational visibility to decisive control. Each layer includes:
- ZTHA Layer – the stage of maturity
- Key Capability – what the organization must be able to do
- Requirement – what “good” looks like operationally
Layer #1 – Visibility
Key Capability: Comprehensive Asset Discovery
Requirement: Discover and map all connected devices (IT, IoT, OT, Shadow IT, USB, etc.), including those invisible to network‑centric tools.
Visibility is the non‑negotiable foundation. Without reliable, continuous knowledge of what is physically connected, every other security control becomes guesswork.
Zero Trust Hardware Access visibility goes far beyond “managed endpoints” or devices with known MAC/IP addresses. It must include:
- Unmanaged devices (no agent, no MDM, no enrollment)
- Silent or dormant devices (not actively generating traffic)
- Non‑traditional devices (USB peripherals, embedded systems, OT controllers)
- Shadow IT devices introduced without approval or process
Outcome:
A continuously updated, normalized inventory and connectivity map of the actual hardware environment – not procurement records, not assumptions, but real‑world presence.
Layer #2 – Identification
Key Capability: Identity Verification
Requirement: Establish asset identity based on inherent characteristics, registered information, and organizational context.
Zero Trust breaks if device identity depends on spoofable claims.
Within Zero Trust Hardware Access, identification means shifting from:
→ “what the device claims it is”
to
→ “what evidence proves it is.”
Identity verification combines:
- Device characteristics – immutable or hard‑to‑fake attributes
- Registered information – what the organization expects to be present
- Organizational context – where it is connected, which segment it belongs to, what function it serves, who owns it, and what role it should play
Outcome:
A defensible, high‑confidence hardware identity record that supports allow/deny decisions and enables downstream policy automation.
Layer #3 – Policy and Postures
Key Capability: Compliance Validation
Requirement: Continuous validation of each device’s behavior, configuration, and overall compliance with security policy.
Once you know what a device is, the next step is determining whether it is allowed to be present and operate in its current state. “Posture” represents the living condition of an asset – how it is configured, how it behaves relative to its expected function, and whether it aligns with defined policy.
This layer introduces ongoing evaluations such as:
- Is the asset operating within its expected role and environment?
- Does it meet required configuration baselines?
- Is it aligned with policy for its location, network zone, and function?
- Has anything drifted? (posture changes over time, whether intentional or malicious)
Outcome:
A continuously refreshed, pass/fail (or graded) posture assessment for every device – not a static snapshot from an annual audit, but a real‑time reflection of compliance and risk.
Layer #4 – Risk Score
Key Capability: Risk Assignment and Scoring
Requirement: Continuous validation of a device’s behavior, configuration, and compliance – used as the evidence base for risk.
Zero Trust Hardware Access treats risk as far more than a static vulnerability list. Instead, risk scoring reflects current, evidence‑based conditions, incorporating insights from Layers 1–3 along with business impact. Effective risk assessment should account for:
- Likelihood – How exposed, suspicious, or non‑compliant the device is
- Impact – Criticality of the device’s location, function, and dependencies
- Confidence – Strength and reliability of the identity and posture evidence
- Urgency – How quickly the device could enable compromise or propagation
Risk scoring is what transforms Zero Trust Hardware Access from pure visibility into defensible operational prioritization – indicating:
- What must be remediated first
- Where enforcement must be immediate
- What can proceed through workflow or review
Outcome:
A ranked, explainable hardware risk list that drives response actions and intelligent resource allocation.
Layer #5 – Control & Enforcement
Key Capability: Access Control and Active Remediation
Requirement: Notify, alert, and actively block unauthorized or non‑compliant devices in real time.
This is where Zero Trust Hardware Access becomes a true control plane – not just identifying issues, but actively reducing exposure. Enforcement must be both timely and actionable, ranging from low‑impact workflows to decisive access denial.
Common enforcement modes include:
- Notify / Alert – Security operations awareness and triage
- Quarantine / Restrict – Temporary access limitation pending investigation
- Deny – Immediate blocking of unauthorized or non‑compliant devices
- Active Remediation – Automated workflows such as tickets, playbooks, or integrated response actions
A core Zero Trust Hardware Access principle:
Enforcement must be based on verified identity + posture + risk, not on assumptions or spoofable indicators.
Outcome:
Real‑time reduction of exposure – unauthorized or non‑compliant hardware is prevented from operating inside the environment.
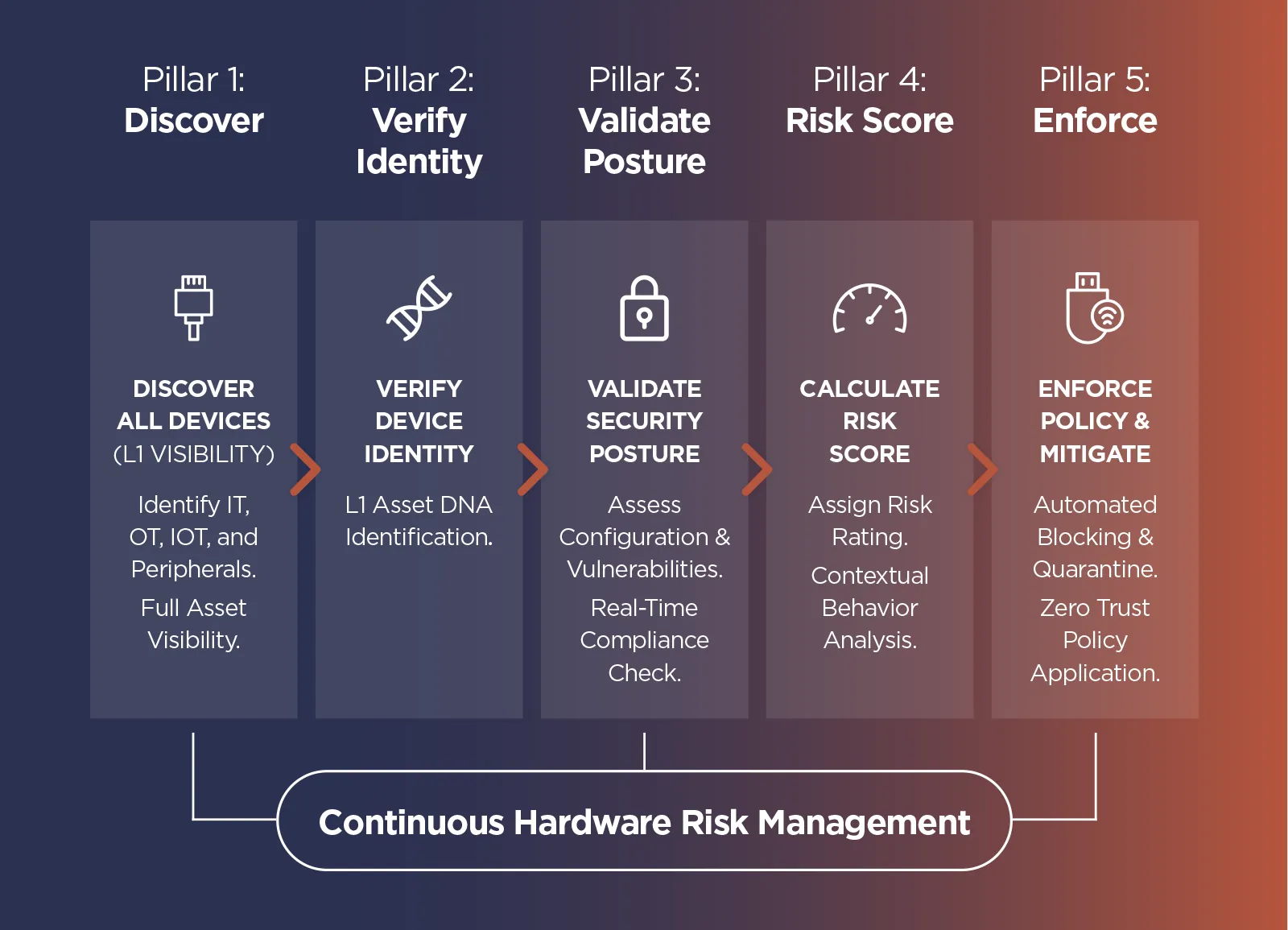
How the Layers Work Together
The Zero Trust Hardware Access framework operates as a continuous, self‑reinforcing loop:
- Visibility ensures nothing is missed.
- Identification transforms inventory into trusted device identity.
- Policy & Posture defines what “good” looks like and checks it continuously.
- Risk turns evidence into actionable prioritization.
- Control & Enforcement reduces exposure and closes the loop with measurable outcomes.
Together, these layers ensure that hardware trust is never assumed – it is continuously verified, validated, and enforced.
Zero Trust Hardware Access With Sepio
With limited device visibility reducing the effectiveness of Zero Trust Architectures (ZTA), enterprises are increasingly shifting their focus toward extending Zero Trust principles down to the hardware layer. By starting at the first – and most fundamental – layer of defense, organizations can establish a more comprehensive Zero Trust Access that strengthens the entire Zero Trust approach.
The Zero Trust (ZT) model grants access based on who, what, when, where, and how. If an organization cannot answer these questions accurately, its Zero Trust Architecture (ZTA) becomes fundamentally ineffective. Achieving this level of assurance requires complete asset visibility.
According to the NIST Zero Trust Architecture framework, authentication and authorization must be enforced before any resource access is granted.
Zero Trust Hardware Access (ZTHA) focuses on all hardware assets operating within the enterprise infrastructure – including remote devices -because these assets originate access requests. Only with full visibility can organizations answer the core Zero Trust questions and enforce policy with precision.
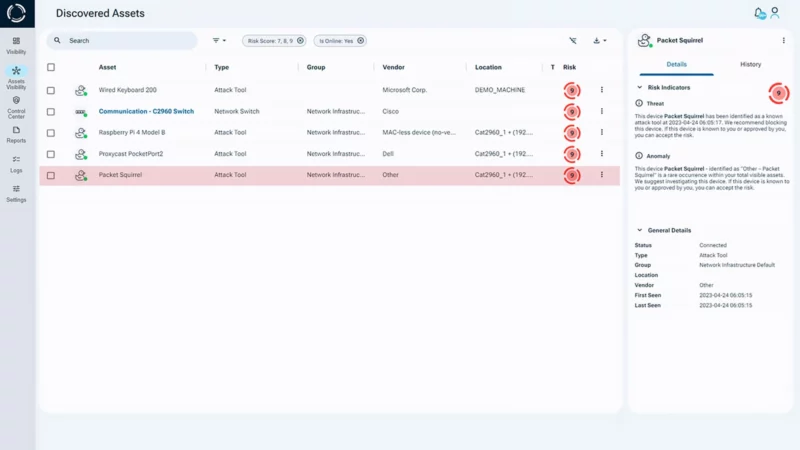
Sepio Visibility Overview
Focusing on hardware significantly strengthens the enterprise’s ZTA, particularly micro‑segmentation efforts. With deep hardware-level visibility, the Policy Engine (PE) can make accurate access decisions based on verified device characteristics rather than assumptions or spoofable identifiers. Additionally, implementing Zero Trust Hardware Access Control (ZTHA) stops a hardware-based attacker at the very first step, preventing them from gaining a foothold or moving deeper into the network.
These approaches align closely with the NSA’s Zero Trust Implementation Guidelines, which emphasize continuous authorization for every user and device.

Sepio’s Hardware Access Control solution enables Zero Trust Hardware Access through a comprehensive, hardware-centric approach. Sepio provides complete device visibility using Physical Layer fingerprinting and Machine Learning, generating a digital fingerprint based on the electrical characteristics of each device. By validating a device’s true Physical Layer identity – not merely its reported attributes – Sepio confirms what a device truly is, not what it claims to be.
Each digital fingerprint is compared against Sepio’s extensive threat‑intelligence database of vulnerable or malicious devices. This allows Sepio to instantly identify when a high‑risk or rogue asset is present in the environment.
Policy Enforcement and Real-Time Mitigation
Sepio’s policy enforcement framework enables administrators to define strict or granular rules that control hardware access based on real device characteristics. These Hardware Access Control policies directly support Principle of Least Privilege (PLP), a core tenet of Zero Trust. When a violation occurs, Sepio automatically triggers mitigation actions – blocking or isolating unapproved or rogue hardware in real time.
By preventing malicious or unauthorized devices from bypassing traditional Zero Trust measures – such as identity‑based approval, traffic inspection, or micro‑segmentation – Hardware Access Control provides decisive, actionable support for Zero Trust Hardware Access and strengthens the overall integrity of the Zero Trust Architecture.
Ready to Strengthen your Zero Trust Architecture?
Talk to one of our experts or book a live demo to see how Sepio delivers complete hardware‑level visibility and control.
Read the Zero Trust Hardware Access White Paper (pdf)





