What Are Shadow IT Assets?
Shadow IT assets are any devices, applications, or services connected to an organization’s network without the knowledge or approval of the IT team.
These can include personal devices, unauthorized software, rogue access points, unmanaged switches, or unapproved cloud services.
The challenge is that these assets operate outside standard security controls. As a result, they create hidden blind spots, making it difficult for IT teams to maintain visibility, enforce policies, and protect the network from potential threats.
As organizations become more decentralized and cloud-driven, the number of shadow IT assets continues to grow, increasing both security and compliance risks.
Shadow IT Asset Risks
Each shadow IT asset increases the organization’s attack surface, introducing new vulnerabilities that attackers can exploit. Without centralized management, IT teams struggle to detect unusual behavior or respond swiftly to threats. This lack of visibility enables prolonged attacker dwell time, raising the risk of data exfiltration, malware infections, and compliance violations.
Unauthorized Network Connections
Unauthorized network connections are one of the primary ways shadow IT assets introduce risk into corporate environments. These connections often bypass security controls and operate outside IT oversight. Here are some examples:
- Personal Devices: When an employee connects a personal router, external drive, or application to the network, it becomes unmanaged. These connections enable file sharing, unapproved software installation, or bypassing security controls. As a result, the risk of data leaks and cyber threats increases.
- Rogue Access Points: Setting up an unauthorized wireless access point, whether for convenience or malicious intent, creates a shadow network connection. This weakens network security, making it easier for attackers to intercept traffic or gain unauthorized access to sensitive systems.
- Compromised Devices: If a network-connected device (such as a printer, IoT device, or server) is infected with malware, it can establish unauthorized connections to external servers. These compromised devices operate outside IT’s visibility, allowing cybercriminals to steal data or launch attacks from within the network.
Shadow IT assets introduce several critical security risks once they connect to the network without proper controls. IT security teams implement strict network configurations and protocols to protect the organization. However, when shadow IT assets bypass these protections, they introduce serious cybersecurity threats, including:
- Security Vulnerabilities: Unauthorized connections often lack firewalls, encryption, or endpoint protection, creating weaknesses that attackers can target.
- Spreading Malware: Shadow IT devices may already be compromised, allowing malware to spread across the network and infect critical systems.
- Data Breaches: Without the right access controls and monitoring, sensitive data can be exposed or stolen, causing compliance violations and financial losses.
These risks grow in regulated industries such as finance, healthcare, and government. Shadow IT can cause serious privacy and data handling violations.
How to Mitigate Shadow IT Asset Risks
To reduce shadow IT risks, organizations must improve network visibility and educate employees about the dangers of unauthorized devices. They should also enforce strict security policies.
This includes conducting regular audits, implementing device control solutions, and fostering a culture of transparency and communication between employees and IT.
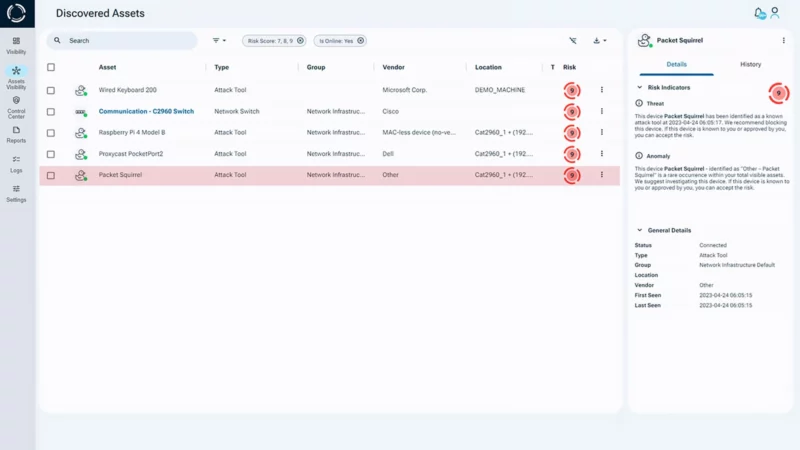
Sepio’s Asset Risk Management (ARM) platform helps organizations gain full network visibility and detect unauthorized connections, reducing the risks posed by shadow IT assets. By securing all network-connected devices, IT teams can minimize the attack surface and protect against potential cyber threats.
Common Shadow IT Scenarios Handled by Sepio
To effectively address these risks, organizations need continuous visibility and control over all connected assets. Sepio helps IT teams detect and mitigate shadow IT through hardware-based visibility, continuous monitoring, and automated reporting. Key scenarios include:
- Rogue Wireless Access Points: Detection of unsupervised or unauthorized access points not managed by the corporate Wireless LAN Controller, preventing unapproved network extensions.
- Unauthorized Wireless Configurations: Identification of random MAC addresses, operational devices on guest Wi-Fi, and BYOD devices on production networks, ensuring proper segmentation and policy compliance.
- Non-Compliant or Risky Devices: Flagging devices with poor reputations, dual-use assets, or personal devices in unauthorized locations, helping enforce corporate device policies.
- Wired Network Misconfigurations: Discovery of unmanaged or unsupervised switches, multiple devices on the same port, or assets operating in incorrect VLANs, reducing exposure of sensitive network segments.
- Rogue Virtual Machines (VMs): Detection of VMs running on unauthorized hypervisors or connected to wrong VLANs, maintaining secure and compliant virtual environments.
Through advanced filtering, tagging, and scheduled reporting, Sepio supports proactive monitoring, early detection, and rapid remediation of shadow IT activity, helping organizations maintain control, visibility, and compliance across their environments.
To support these capabilities, Sepio combines endpoint-level enforcement with deep network visibility.
At the endpoint level, the Sepio Agent provides lightweight, hardware-based protection with minimal system impact. It enables granular control over USB and peripheral usage, allowing only approved devices while blocking unauthorized ones. This prevents the use of rogue removable media, one of the most common vectors for malware and data exfiltration, without disrupting user productivity.
Hardware-Level Visibility and Continuous Asset Intelligence
At the network level, the Sepio Scan Engine continuously identifies and profiles all connected hardware by interacting directly with network infrastructure using secure protocols. Designed for scalability, it delivers detailed asset intelligence across complex environments and maintains up-to-date inventories through frequent scanning.
Unlike traditional discovery tools that rely solely on software-based identification, Sepio uses hardware fingerprinting to detect devices based on their physical characteristics. This ensures that even spoofed, hidden, or otherwise disguised assets are accurately identified.
By combining continuous monitoring with hardware-level visibility and control, Sepio enables organizations to detect, manage, and eliminate shadow IT assets before they evolve into serious security incidents.

Manage Your Network Devices Effectively
Gaining full visibility into network devices is crucial for eliminating blind spots caused by shadow IT assets. By using physical layer data, organizations can detect and mitigate unauthorized devices that traditional security solutions overlook.
With Sepio, IT teams are empowered to make informed decisions, reduce risk exposure, and strengthen their overall cybersecurity posture.
Shadow IT is not just a security problem; it is also a business challenge. Understanding and addressing shadow IT enables organizations to maintain trust, meet compliance standards, and ensure smooth operations.
Schedule a demo to see how Sepio identifies hidden shadow IT assets, enforces policy, and helps secure your network in real time.








