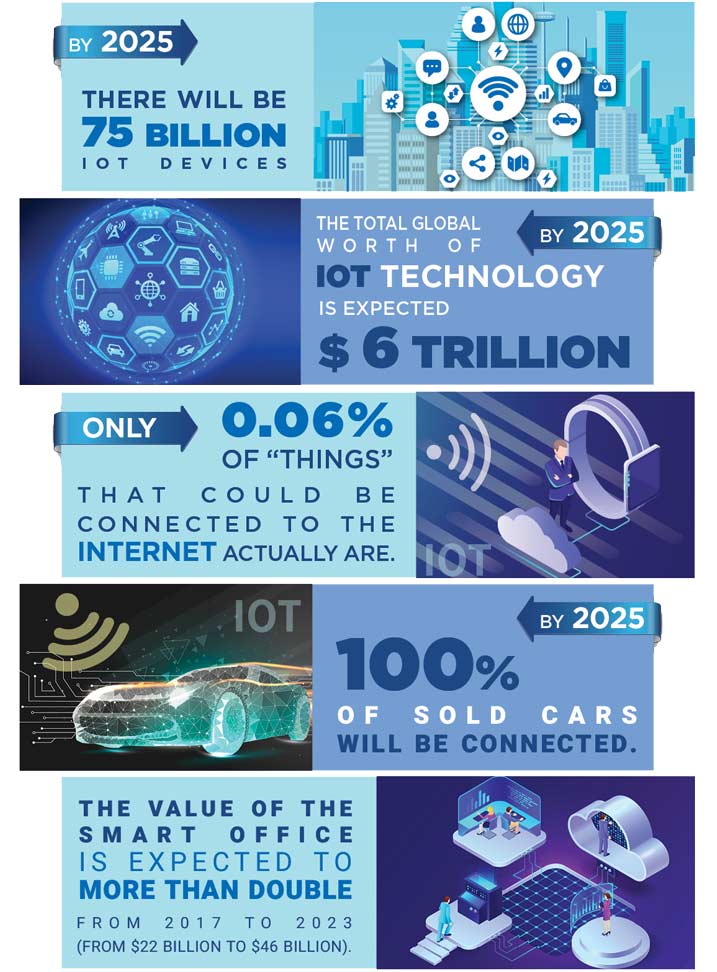
Internet of Things (IoT) devices bring convenience, efficiency, and connectivity, but they also introduce significant security risks. From smart home gadgets to enterprise IoT deployments, every connected device expands the attack surface and creates new entry points for cyber threats.
As Black Friday and the holiday season approach, it’s worth considering the hidden risks behind new tech purchases. A smartwatch, smart speaker, or connected camera may improve everyday life, but are these IoT devices secure? While traditional cybersecurity measures, such as network security, antivirus tools, and strong passwords, remain essential, they are no longer sufficient on their own to address today’s evolving IoT threats.
Unlike traditional endpoints, many IoT devices are designed with convenience and cost-efficiency in mind rather than security. Limited built-in protections, infrequent firmware updates, and lack of visibility make them attractive targets for attackers.
Common Risks Posed by IoT Devices
Our reliance on connected technology continues to grow. Devices like smartphones, smart lighting, surveillance systems, printers, medical devices, and baby monitors are now embedded in both personal and professional environments. However, each connected device can also serve as a potential entry point into a network.
IoT-specific risks include:
- Weak or default credentials that are rarely changed
- Unpatched vulnerabilities due to infrequent updates
- Lack of device visibility within the network
- Insecure communication protocols
- Physical access vulnerabilities, which are often overlooked
To illustrate, imagine inviting someone into your home. While you step away briefly, they connect a malicious USB device to one of your systems. Hours later, unusual behavior begins, devices activate unexpectedly, systems behave erratically, and control appears compromised. What seems like a technical glitch is actually the result of a hardware-based attack.
This scenario highlights a critical but often overlooked risk: attackers can exploit physical access to introduce rogue devices, establish backdoors, and move laterally across connected systems. While it may sound extreme, such attacks are entirely feasible and increasingly relevant.
Additionally, IoT devices can be recruited into botnets without the owner’s knowledge. Compromised devices may be used to launch large-scale Distributed Denial-of-Service (DDoS) attacks, mine cryptocurrency, or act as persistence points for long-term espionage.
Risks of IoT Devices in Organizations
In enterprise environments, the risks become even more pronounced. Bring Your Own Device (BYOD) policies, while convenient and cost-effective, increase exposure by allowing personal devices to connect to corporate networks.
Employees often connect personal smartphones, wearables, or home-connected devices to corporate resources, sometimes indirectly through VPNs or remote work setups. Each connection creates a potential bridge between secured enterprise infrastructure and less secure consumer ecosystems.
A compromised IoT device can quickly become a gateway to sensitive business data. Once inside, attackers can pivot to employee-owned devices, access confidential information, and expand their reach across the organization.
Key organizational risks include:
- Unauthorized device access to corporate networks
- Data exfiltration through compromised endpoints
- Shadow IT and unmanaged devices
- Expanded attack surface due to remote work environments
- Compliance and regulatory challenges
With the average household containing dozens of connected devices, employees working remotely introduce a large number of unmanaged endpoints into the corporate threat landscape. This significantly increases the complexity of maintaining visibility and control.
IoT Risks Across IT, OT, and IoT Environments
IoT risks are not limited to traditional IT networks. They also extend into Operational Technology (OT) environments such as industrial control systems, manufacturing equipment, and critical infrastructure.
In these environments, compromised devices can have real-world consequences, including:
- Disruption of industrial processes
- Downtime in manufacturing operations
- Safety hazards in critical infrastructure
- Financial and reputational damage
Unlike IT systems, OT environments often rely on legacy devices that were never designed with security in mind. Integrating IoT into these environments without proper controls further amplifies the risk.
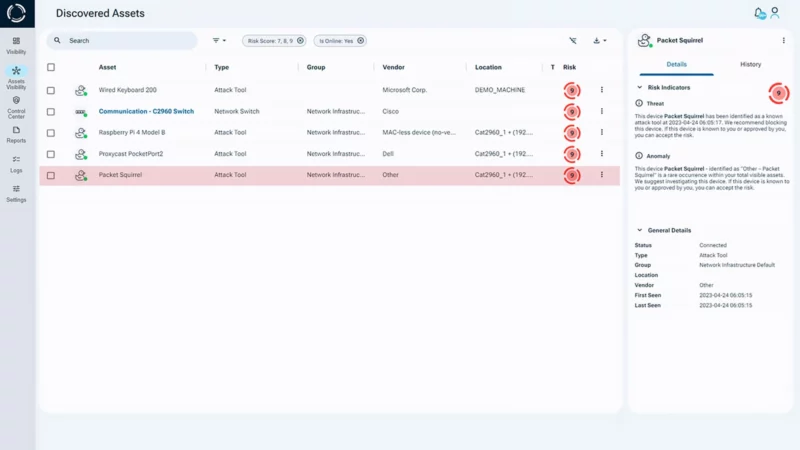
Identifying Covert Hardware Threats
One of the biggest challenges in mitigating IoT risks is detecting hardware-based attacks. Rogue devices, such as malicious USB drives, network implants, or spoofed peripherals, can easily bypass traditional security controls because they operate below the visibility of software-based defenses.
These threats often go undetected due to limited Layer 1 visibility. Security tools that rely on software agents or network monitoring may not recognize a device that masquerades as legitimate hardware.
For example:
- A malicious USB device can appear as a keyboard or network adapter
- A hardware implant can intercept or manipulate network traffic
- A spoofed device can mimic trusted equipment to avoid detection
Because these attacks originate at the physical layer, they are effectively invisible to many traditional defenses. Their legitimate appearance raises no suspicion, allowing attackers to establish persistence without triggering alerts.
Why Traditional Security Falls Short
Traditional cybersecurity solutions focus heavily on software and network behavior. While they are essential, they often miss threats that originate at the hardware level.
Common gaps include:
- No visibility into physical device identity
- Inability to detect spoofed or unauthorized hardware
- Delayed detection after compromise has occurred
- Limited control over device-level access
As attackers increasingly exploit these blind spots, organizations must extend their security strategies beyond software and network layers.
How Sepio Mitigates IoT Risk
Sepio addresses these challenges by providing a hardware-first approach to cybersecurity, delivering full visibility at the physical layer.
Using Layer 1 fingerprinting, Sepio creates a unique digital identity for every connected device across IT, OT, and IoT environments. This enables accurate, tamper-resistant device identification regardless of how a device presents itself.
With this approach, organizations can:
- Detect spoofed or rogue USB devices
- Identify hidden or unauthorized hardware implants
- Gain complete visibility into all connected devices
- Enforce granular device-level security policies
- Prevent lateral movement across the network
Sepio’s Rogue Device Mitigation capability automatically blocks unapproved or suspicious hardware before it can establish a foothold. By stopping attacks at the earliest stage, before they propagate, organizations can significantly reduce their risk exposure.
This level of visibility also enhances existing security investments by providing accurate device context to other security tools, strengthening the overall security posture.

Protect Your Network from IoT Risks
IoT devices are here to stay, but so are the risks they introduce. Securing these environments requires more than traditional defenses. It demands visibility into the physical layer where many advanced threats originate.
By addressing hardware-level risks, organizations can close critical security gaps, prevent unauthorized access, and maintain control over their connected environments.
Discover how Sepio helps organizations secure IT, OT, and IoT ecosystems with complete hardware visibility and control.
Schedule a Demo to see how you can reduce IoT risk and prevent unauthorized access.









