What Are Social Engineering Attacks?
Social engineering attacks are deceptive tactics used by cybercriminals to manipulate individuals into revealing confidential information, granting system access, or performing actions that compromise security. Unlike traditional cyberattacks that rely on software vulnerabilities, social engineering exploits human behavior, trust, fear, curiosity, or urgency, to breach organizational defenses.
These attacks take many forms, from phishing emails and fake tech support calls to more advanced tactics involving rogue hardware. Whether carried out digitally or physically, the goal is the same: trick people into opening the door to the attacker, sometimes literally.
Why Social Engineering Attacks Are So Effective?
Social engineering attacks succeed because they prey on predictable human responses. People tend to trust familiar-looking devices, obey perceived authority figures, or respond hastily to urgent-sounding requests. Cybercriminals exploit these tendencies to bypass even the most advanced technical security measures.
For example, an employee might click on a seemingly innocent link in a well-crafted phishing email or plug in a USB drive labeled “Payroll Q2” they found in the parking lot. These actions, driven by curiosity or urgency, are precisely what attackers count on.
Employees: The Prime Targets of Social Engineering Attacks
Despite investments in cybersecurity, employees continue to represent the most exploited entry point for attackers. Most training programs focus on phishing alone, but social engineering attacks have evolved far beyond email scams. Today, cybercriminals also use hardware-based social engineering tactics to infiltrate networks, often without employees realizing they’ve been manipulated.
The Role of Rogue Devices in Social Engineering Attacks
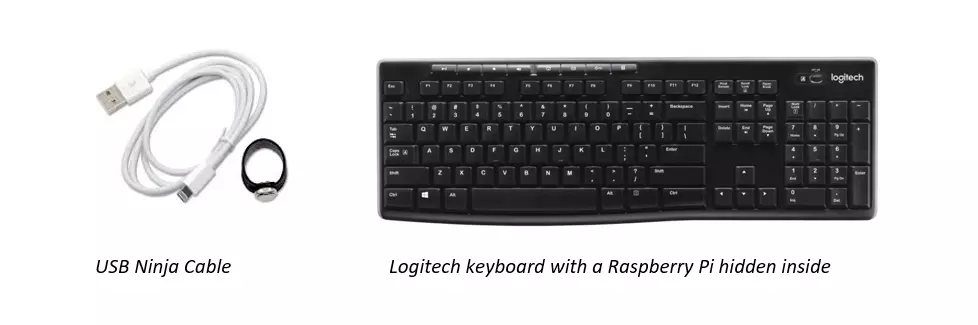
One of the most deceptive forms of social engineering is the use of rogue devices, hardware attack tools designed to appear legitimate. These devices often mimic everyday office items like USB chargers, keyboards, or mice. They are specifically crafted to evade suspicion, providing cybercriminals with an easy way to launch attacks without detection.
For example, a Ninja Cable (a USB cable used for “juice jacking”) may look like an innocent charger, but it is capable of stealing data and injecting malware. Similarly, a Raspberry Pi embedded inside a keyboard could give attackers access to systems with minimal risk of detection. When devices that seem benign are actually hidden attack tools, the threat becomes far more dangerous.
How Social Engineering Enables Hardware-Based Attacks
Social engineering attacks often provide the necessary access for deploying rogue devices. Attackers may impersonate delivery personnel, cleaners, or even employees to infiltrate a workplace. These tactics exploit social norms, few employees challenge a person in a uniform or someone who “just forgot their badge.”
Once inside, the attacker can discreetly plug in a malicious device. Because traditional security solutions lack visibility at the physical layer, these hardware-based social engineering attacks often go undetected until it’s too late.
Exploiting Remote Access Through Social Engineering
The attack surface has widened significantly with the rise of Bring Your Own Device (BYOD) and remote work. Today, social engineering attacks no longer require physical presence. Cybercriminals manipulate users into connecting rogue devices at home, devices that may have been purchased unknowingly from online marketplaces like Amazon or AliExpress.
Even public charging kiosks have become attack vectors. This tactic, known as “juice jacking,” involves loading malware onto devices when they are plugged in to charge. Some attackers have gone as far as distributing free USB drives or chargers disguised as promotional gifts, knowing that the temptation of a giveaway is often enough to override caution.
In one case, an attacker mailed a $50 Best Buy gift card along with a USB drive to a hospitality company. Fortunately, the recipient grew suspicious, either through training or intuition, and avoided a potentially devastating breach.
How to Prevent Hardware-Based Attacks
Traditional security solutions, such as Network Access Control (NAC), Endpoint Protection Systems (EPS), and Intrusion Detection Systems (IDS), often fail to detect Rogue Devices because they lack Layer one visibility, the ability to identify physical devices on a network. This lack of visibility makes it essential to have a security solution that can detect, identify, and block Rogue Devices before they can infiltrate your network.
While training and awareness are important tools for preventing social engineering attacks, they are not foolproof. Employee negligence remains a significant factor in 62% of cyber incidents. Therefore, organizations need a comprehensive solution to complement human awareness.
The Solution: Sepio’s ARM Platform
To mitigate the risks associated with hardware-based social engineering attacks, Sepio’s Asset Risk Management (ARM) platform provides real-time visibility into your network’s physical layer. This allows your organization to detect and block Rogue Devices before they can cause harm.

With Layer 1 visibility and advanced detection capabilities, Sepio’s platform ensures that even the most covert hardware attacks are caught early, allowing organizations to defend against threats that traditional cybersecurity solutions miss.
See How Sepio Prevents Hardware-Based Attacks
Social engineering attacks don’t stop at phishing, they now include covert hardware-based threats that bypass traditional security tools. Sepio’s Asset Risk Management platform provides unmatched Layer 1 visibility to detect and block rogue devices before they infiltrate your network.
Schedule a demo today to see how Sepio protects your organization against hardware-based social engineering attacks.