Managing Raspberry Pi device risks is crucial when utilizing this small, inexpensive, and portable computer. Despite its ability to perform tasks similar to any regular computer, such as browsing the internet, playing high-definition videos, and handling word processing or spreadsheets, it’s important to recognize and mitigate potential security risks. Proper risk management ensures safe use of Raspberry Pi, protecting it from vulnerabilities in various applications.
Initially designed for ethical purposes, the Raspberry Pi’s versatility makes it a popular choice for educational, personal, and industrial applications. However, it can be exploited for malicious purposes, such as cyberattacks and unauthorized access. Effective Raspberry Pi device management helps mitigate these threats, especially in sensitive environments, and maintains strong security controls.

Raspberry Pi Device Risks and Security Challenges
PoisonTap
PoisonTap, designed for Raspberry Pi, creates a cascading effect by exploiting the inherent trust in various machine and network mechanisms, leading to extensive information exfiltration. It enables network access and installs semi-permanent backdoors.
P4wnP1
The P4wnP1 platform transforms a Raspberry Pi into a USB attack device, enabling harmful activities like keystroke injection and unauthorized system access. It can bypass security protocols and act as a rogue device in corporate networks.
Bypassing NAC
NAC software supports network visibility and access management through policy enforcement on devices and users of corporate networks. To bypass, an attacker must access a device that has already been authenticated. In other words, a genuine device must be spoofed, which a Raspberry Pi can do.
The authenticated device is used to log into the network which then smuggles network packets from the Raspberry Pi by overwriting the MAC address. Making it seem as if the packets are originating from the genuine, authenticated device. From here, the attacker has access to the organization’s network and can, consequently, move laterally through it. This can allow for a variety of potential attacks such as a data breach, malware installation or Advanced Persistent Threat (APT) attack.
Advanced Persistent Threats with Raspberry Pi
An Advanced Persistent Threat using a Raspberry Pi is a significant Raspberry Pi security concern for government agencies and critical infrastructure. These state-sponsored attacks can infiltrate networks undetected, exfiltrate data, and threaten national security. Because of the low cost and high impact of these devices, they are often favored for sabotage in cyberwarfare.
Raspberry Pi Risks and IoT
Raspberry Pi devices are sometimes used in medical equipment, such as ventilators. Their low cost, portability, and computing capabilities make them attractive for healthcare use. However, this increases Raspberry Pi network security risks by adding more entry points for attackers in one of the most targeted sectors.
Healthcare networks, already under strain, often overlook cybersecurity. PHI (Personal Health Information) is highly valuable to cybercriminals, and Raspberry Pi vulnerabilities can be a gateway to larger breaches. This highlights the need for strong Raspberry Pi device management within IoT environments.
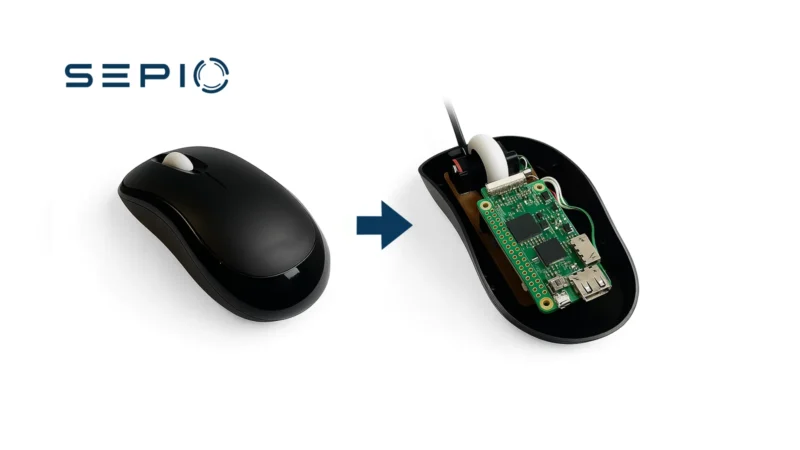
Raspberry Pi Risks in Network Security
The Raspberry Pi’s clandestine nature is one of the major risks associated with the device (Pi400 is it 100x safer than Pi4?). Its small physical size allows it to be discreetly embedded within peripherals or introduced into the network, evading human detection.
When employed as a USB attack tool, security software solutions identify the device as a legitimate HID device. Thereby raising no alarms. When acting as a network implant, the device sits on the Physical Layer. Which existing security software solutions do not cover. This means it can remain completely unnoticed, posing a critical Raspberry Pi network security risk.
Network Assets Visibility
Enterprises often lack network visibility into connected hardware assets, particularly across complex IT, OT, and IoT infrastructures. This blind spot weakens policy enforcement and increases the risk of ransomware attacks, data breaches, and insider threats.
To address this challenge, organizations must gain complete visibility into all hardware assets—regardless of their type or the interface used to connect them. Threat actors frequently exploit these visibility gaps using USB Human Interface Device (HID) emulation tools or physical layer network implants that evade traditional security controls.
Visibility alone, however, is not enough. It must be backed by robust policy enforcement. Administrators need the ability to define and enforce granular control policies that adapt to changing cyber threats and ensure strong protection across all hardware endpoints.
Managing Raspberry Pi Risks with Sepio
Sepio is the leader in the Rogue Device Mitigation (RDM) market and is changing the cybersecurity industry by Identifying hidden hardware attacks operating over network and USB interfaces. Sepio’s solution identifies, detects, and manages all peripherals, no device goes unmanaged.
The only company in the world to undertake Physical Layer Visibility fingerprinting, Sepio calculates a digital fingerprint using the device descriptors of all connected peripherals and compares them against a known set of malicious devices, automatically blocking any attacks. With Machine Learning, the software analyses device behavior to identify abnormalities, such as a mouse acting as a keyboard.
Complete Visibility of all Hardware Assets
With all devices and anomalies detected, enterprises benefit from a greater overall cybersecurity posture. Gaining full visibility of all hardware devices from endpoint peripherals to connected devices (IT/OT/IoT). Sepio uses unique physical layer hardware fingerprinting technology and data augmentation from endpoints and networks.

Full Control through Predefined Policies: Enterprise-wide policies enable compliance, regulation and best practices. With predefined templates and no whitelisting, and no requirement for a clean environment start, Sepio provides a fast and easy setup.
Rogue Device Mitigation (RDM): Threat mitigation upon discovery of rogue or threatening devices. Integrations with existing security platforms such as NACs and SOARs for mitigation.
Talk to an expert. It will help you understand how to use Sepio’s patented technology to gain control of your asset risks.
Read the Raspberry Pi – A Friend or Foe? white paper (pdf)