Printer Security Risks
Printer security risks are a growing concern in today’s interconnected environments. As IoT devices, printers are often overlooked, yet they present significant vulnerabilities that cybercriminals are eager to exploit. These printer security vulnerabilities can lead to unauthorized access, data theft, and full-scale network infiltration. Ignoring these risks can leave your organization exposed to cyber-attacks that compromise sensitive information and disrupt operations.
Because printers are often connected to the same network as critical systems, they pose a significant network printer security risk, making them potential entry points for unauthorized access, data theft, and deeper network infiltration. Securing printers is essential to prevent them from becoming gateways for broader cyber-attacks that could compromise the entire infrastructure.
Are Printers a Security Risk?
Printers are no longer simple standalone devices; they process, store, and transmit data, making them vulnerable to cyber threats. Connected to the same networks as critical infrastructure, printers pose network printer security risks that attackers can use to gain unauthorized access, exfiltrate data, or spread malware across the organization.
Are printers a security risk? Absolutely. Most organizations fail to implement strong printer security measures, leaving these endpoints exposed. According to a Spiceworks survey, only 16% of IT professionals consider printers to be at high risk, and 43% don’t include printers in their endpoint security strategy, highlighting a major gap in protection.

Why Printers Are an Attractive Target for Attackers
Every organization will have multiple printers at the office and are therefore an appealing target for malicious actors. Printers are common targets in bank cyber attacks due to numerous vulnerabilities, but all organizations are at risk.
Printer security risks are often underestimated because the devices themselves seem innocuous. However, their integration into the network means they are as critical to protect as servers and computers. Attackers are aware of this gap in security and often exploit it to launch attacks. For example, hackers can use compromised printers to intercept sensitive documents, alter print jobs, or launch more extensive network infiltration.
Printer security goes beyond setting passwords or using basic encryption. It requires a comprehensive approach, including regular firmware updates, network segmentation, and robust access controls. Organizations should treat printers like any other network endpoint, conducting regular security assessments and monitoring for potential threats.
Printer Security Vulnerabilities
Understanding the specific printer security risks your organization faces is essential for mitigating them effectively:
Document Theft
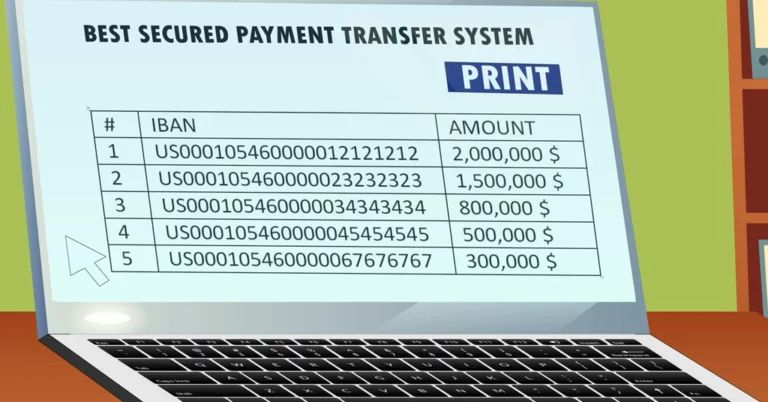
Printers store scans, faxes, and print jobs. If accessed by a hacker, these documents can be stolen and sold on the dark web, leading to regulatory violations and reputational damage (Source: The State of Printer Security).
Changed Settings
An hacker can manipulate a printer’s settings to reroute print jobs, gaining access to confidential information. They may also open saved copies of sensitive documents or reset the printer to factory defaults, wiping out all organizational and security setup. Such changes can lead to severe data leaks and compromise your entire network.
Eavesdropping
Another critical printer security vulnerability is eavesdropping. In this case, an attacker can intercept and capture documents sent from the computer to the printer. By sitting on the network, an implant can gain access to the network printer traffic using Man-in-the-Middle attacks (MiTM), and obtain potentially sensitive information.
Network Infiltration
By gaining access to a network connected printer, an hacker can move laterally across the network to other unsecured devices. This lateral movement often causes more damage than an attack limited to the printer itself. Even if sensitive data isn’t found on the printer, the hacker can use it as an entry point to access the network, locate private information elsewhere, and expand their reach undetected.
DDoS Attacks
Printers can be compromised and added to botnets used for DDoS attacks, potentially disabling devices and networks.
Malware Installation
Printers are susceptible to malware, which can provide persistent access for hackers and serve as a base for future attacks.
Printer Security Risks in IoT Environments
IoT printers are especially vulnerable to hardware attacks attacks, such as rogue implants operating at the physical layer. These stealth threats bypass traditional security solutions, making printer security vulnerabilities even harder to detect.
Printers’ seemingly innocuous nature contributes to their neglect in security planning. Yet, this is precisely what makes them an attractive target, cybercriminals know they can exploit these weak points without triggering alarms.
How Sepio Mitigates Printer Security Risks
Heavy spending on cybersecurity should bring a high return on investment, yet gaps in visibility limit this. Sepio’s asset risk management (ARM) platform provides a panacea to gaps in device visibility to ensure you are getting the most out of your cybersecurity investments. Sepio’s integrates with existing solutions, such as NAC, EPS, SIEM and SOAR, enhancing computer-security and data-security.

Sepio’s asset visibility capabilities ensure no device goes unmanaged. The platform identifies, detects, and manages all IT, OT, and IoT devices seamlessly. Additionally, Sepio’s policy enforcement and rogue device mitigation features instantly block any unauthorized or rogue hardware. This empowers a Zero Trust Hardware Access (ZTHA) approach, strengthening your printer security and stopping hackers at the very first line of defense.
Take Action to Protect Your Printers
Printers are frequently the weakest link in an organization’s security chain. Don’t let cybercriminals exploit these information security gaps. Strengthen your defenses by partnering with security experts and safeguard your network against malware, phishing, and other cyber threats. (Watch Sepio video: Printer Hacked).
See every known and shadow asset. Prioritize and mitigate risks. Talk to an expert to understand how Sepio’s technology can secure your printers and protect against cyber threats.