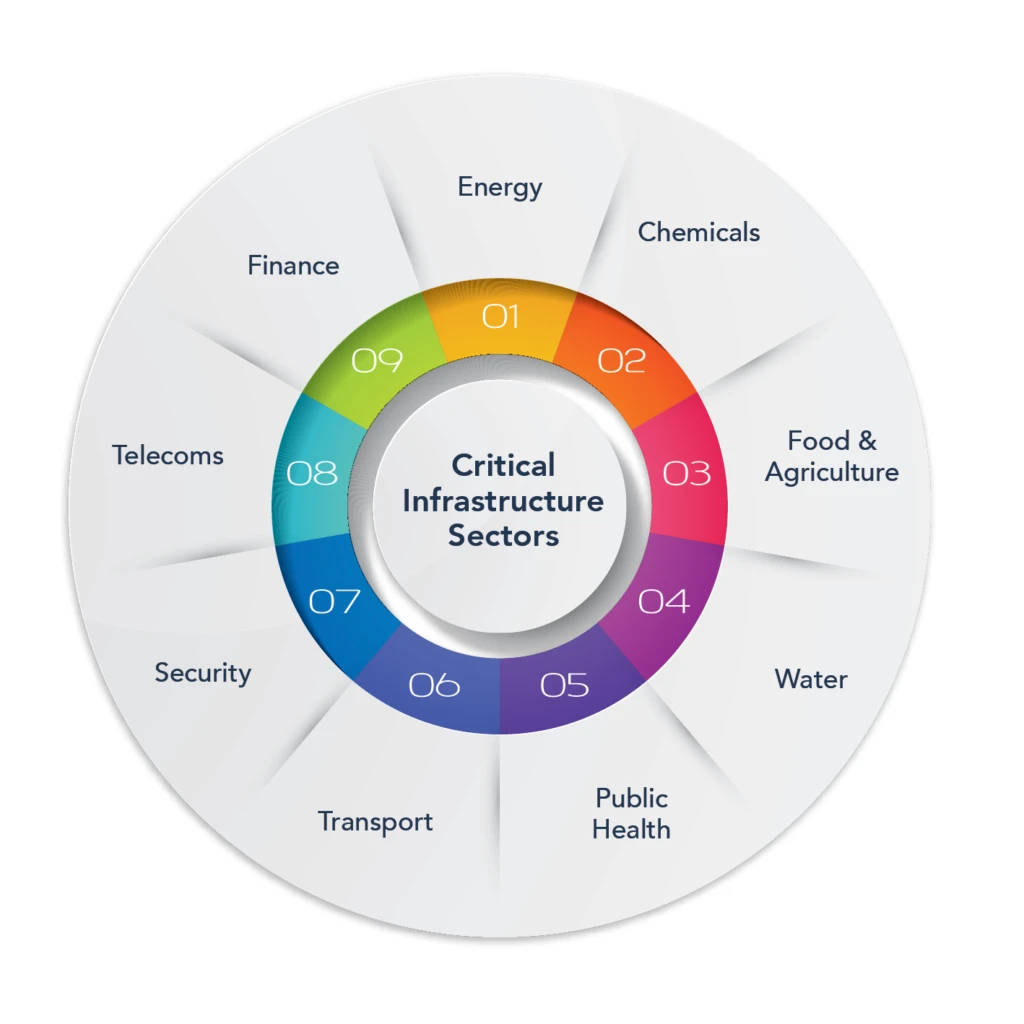
Critical infrastructure cybersecurity focuses on protecting the systems, assets, and services that support energy, water, healthcare, transportation, and other essential sectors. Because these environments combine IT, OT, IoT, and unmanaged devices, they face heightened cyber risks, ransomware, supply‑chain compromise, rogue devices, and operational disruption. This guide explains the core challenges of critical infrastructure cybersecurity and the controls needed to secure complex, distributed environments.
What is Critical Infrastructure Cybersecurity?
Critical infrastructure cybersecurity refers to the tools, processes, and controls that protect essential services, such as energy, water, healthcare, and transportation, from cyberattacks. It includes securing IT and OT networks, validating connected devices, preventing rogue or spoofed hardware, and ensuring operational resilience against threats that could disrupt public safety or economic stability.
Why Does Cybersecurity for Critical Infrastructure Matter?
Critical infrastructure supports the economy, public health, and national security. Without it, modern life would stop. As a result, a cyberattack on a power grid or water plant can cause widespread harm. It can shut down services, create panic, and put people in danger.
Moreover, hackers may target these systems to steal information, demand ransom, or cause disruption. Because of this, protecting critical infrastructure has become a national priority.
Types of Cyberattacks on Critical Infrastructure
Cybercriminals use different methods to attack. Some of the most common are:
- Malware: software that damages or disables systems.
- Phishing: fake emails that trick people into giving sensitive information.
- Data leaks: exposure of confidential files.
- Unauthorized access: hackers breaking into systems they shouldn’t reach.
These attacks can stop operations, steal data, and cause serious damage. To fight these threats, governments and companies must boost cybersecurity. In today’s digital world, defending critical infrastructure is more important than ever. It is protecting, public safety, the economy, and national security.
Critical Infrastructure Cybersecurity Challenges
Outdated Systems
Many critical infrastructure systems still use old technology. For example, programmable logic controllers often don’t have strong security. These systems were not built with cybersecurity in mind. Thus, they are an easy target for hackers.
IoT Devices and a Larger Attack Surface
One big challenge is the growing number of connected devices. The rise of Internet of Things (IoT) devices in infrastructure adds more ways for attackers to get in. While IoT improves how things work, it also increases security risks. Without the right protection, hackers can use these devices to access networks.
Human Error
Human error is still one of the top cybersecurity risks. Employees are often the weakest link in the security chain. Without the right training, they can fall for scams or ignore security rules.
To lower this risk, organizations should:
- Build a strong security culture.
- Provide regular cybersecurity training.
- Have a clear plan for dealing with incidents.
Connected Control Systems
Industrial Control Systems (ICS), like SCADA and DCS, have changed over time. Today, with the rise of Industrial IoT, these systems connect to outside networks. That makes Operational Technology (OT) cybersecurity more important than ever. Hackers can now reach systems that were once isolated.
Asset Visibility in Critical Infrastructure
You can’t protect what you can’t see. That’s why knowing every device on your network is vital. This includes hardware in IT, OT, and IoT environments. A full inventory allows for better control and faster threat response.
Additionally, monitoring connected hardware assets at the physical layer is critical for infrastructure cybersecurity. It helps detect hardware attack tools before they can cause damage.
How Sepio Strengthens Critical Infrastructure Cybersecurity
Sepio provides hardware‑based asset intelligence that strengthens critical infrastructure cybersecurity by identifying, validating, and monitoring every device across IT, OT, IoT, and IoMT environments. This includes detecting rogue, spoofed, or unmanaged devices that traditional tools miss, enabling operators to reduce operational risk, improve compliance readiness, and prevent malicious
Hardware-based attacks are harder to detect and can bypass traditional software tools. Sepio provides physical layer visibility so you can see and manage every connected device.
Sepio leads in Rogue Device Mitigation (RDM). It is the only company in the world that checks and controls every network device.
Sepio offers a comprehensive platform for:
- Rogue Device Mitigation (RDM): Stops unapproved devices.
- Zero Trust Hardware Access (ZTA): Trust nothing by default, verify every device.
- Policy enforcement engine: Set strict rules and get alerts when they’re broken.
If a device breaks a rule, Sepio blocks it right away. This provides hardware security and keeps critical infrastructure safe from hardware-level threats.

Critical Infrastructure with Strong Security
Critical infrastructure and cybersecurity are vital to national safety. As hardware attacks grow more advanced, governments must act quickly. That means having strong policies and using hardware security platforms like Sepio.
Fighting cybercrime is an ongoing battle. But with the right tools, organizations can stay protected. Sepio’s advanced tech secures hardware at the physical layer, keeping critical infrastructure strong against attacks.
Sepio reduces hardware risks by finding rogue devices in real time. In today’s world, this kind of protection isn’t just helpful, it’s essential.
- To learn more about CISA Critical Infrastructure Sectors.
- To learn more about EU Critical Energy Infrastructure and its cybersecurity.
Strengthen Your Critical Infrastructure Cybersecurity
Cyber threats are growing fast. That’s why it’s crucial not to fall behind. Sepio’s technology gives you full visibility into your hardware assets so you can focus on the most urgent risks.
The platform also offers ongoing protection against hardware-level threats. This boosts your overall cybersecurity strength and helps stop unauthorized access.
Strong cybersecurity is key to protecting national security. Talk with one of our security experts today to learn how Sepio can block rogue devices and defend your infrastructure. Act now to stay secure.






