Cybersecurity in Healthcare
Hardware in healthcare poses cybersecurity risks. Are you aware of these risks in UK healthcare? It is no secret that healthcare facilities hold important patient data. And, with the UK’s National Health Service (NHS) caring for over 1 million patients every 24 hours, one can only imagine the amount of data that one working day can produce. Additionally, healthcare data comes with a big price tag on the dark web, more than any other data. According to a report, a healthcare data record can be valued at around £200, compared to just £4 for the next highest value record (a credit/debit card). With access to such an abundance of highly valuable data, the NHS, as well as private healthcare entities, are major targets for malicious cyber criminals.
In 2017, the NHS suffered one of the most infamous cyber incidents in history: the Wannacry ransomware attack. This prompted NHS facilities to reassess their cybersecurity in healthcare strategies. In 2019, Matt Hancock, the Secretary of State for Health and Social Care, established NHSX; a government unit responsible for developing best practice for NHS technology. Nevertheless, this industry as a whole, not solely the NHS, is still severely lacking in sufficient healthcare IoT security. This is perilous considering the industry’s reliance on technology is only expanding. Moreover, COVID-19 has expedited this dependency, making cybersecurity in healthcare more crucial than ever.
Cybersecurity Risks in the Healthcare Industry
As mentioned, the most significant attack on the UK’s healthcare industry occurred in 2017. Although only lasting a few days, the Wannacry attack affected up to 70,000 NHS devices. This includes computers, MRI scanners, blood-storage refrigerators and theatre equipment. Because of the necessity of connected medical devices, some NHS services had to turn away non-critical emergencies, divert ambulances, and cancel 19,000 appointments. Understandably, this caused complete chaos and cost the UK £92 million.
Despite this wake-up call, progress has been insufficient. Research by ForgeRock identified healthcare as the most at-risk sector in the UK. Additionally, Clearswift reported that two-thirds of UK healthcare bodies experienced a cybersecurity incident, highlighting the ongoing vulnerability of cybersecurity in healthcare.

The Appeal of Hardware Attacks on Healthcare Facilities
Cybercriminals and nation-state actors increasingly target healthcare facilities. According to the National Cyber Security Centre (NCSC), over a quarter of UK cyber incidents in 2020 exploited pandemic-related vulnerabilities.
With the UK treating tens of thousands of patients daily, attackers are motivated by valuable data that can be sold on the dark web. Advanced Persistent Threat (APT) groups exploit these conditions to steal intellectual property, including vaccine research, making UK healthcare a high-value target.
Cybersecurity Risks Using COVID-19 Tracking Apps
Moreover, COVID-19 tracking apps are another cause for concern in the realm of cybersecurity. These apps provide more than just an individual’s healthcare information. Using contact tracing to curb the spread of the virus, the apps collect information on where an individual has been and who they have been in contact with. This information can be useful for state-sponsored groups conducting espionage activities. This is especially if they target high value individuals such as politicians. To make matters worse, researchers found seven security flaws in the UK’s pilot app. These flaws are unsurprising, given that the healthcare industry’s main focus was combating the virus, leaving healthcare cybersecurity even more neglected.
The greatest problem associated with the lack of cybersecurity in the healthcare industry is that an attack can be fatal. With so many devices and operations becoming more reliant on technology, including those which perform life-saving actions, an attack could directly, and indirectly, result in many patient deaths.
Why Healthcare Facilities Are Vulnerable to Cybersecurity Threats
Hardware Attacks Targeting Medical Devices
With the appeal of an attack on a healthcare organization being high, and the reliance on technology within the sector increasing, attackers are turning to hardware-based attacks. These attacks have greater chances of success due to a lack of hardware security. Spoofed Peripherals impersonate legitimate Human Interface Devices (HID) and therefore do not raise alarms, while Network Implants sit on the Physical Layer which is not covered by existing security software solutions. Rogue Devices have the ability to conduct harmful attacks that can result in data theft, espionage and operational disruptions meaning that their extremely covert nature makes them a major threat due to the extent of damage that they can cause.
Lack of Cybersecurity Investment in Healthcare
With healthcare entities performing life-saving operations, cybersecurity is often deemed a hindrance to the time-critical nature of the industry. The healthcare sector has a reputation of neglecting cybersecurity in favour of patient care. This is not necessarily a negative approach, yet when patient care is relying on technology, a lack of cybersecurity is, in fact, detrimental to the industry’s very cause. UK healthcare providers are not allocating enough of their budget to cybersecurity, resulting in insufficient measures and an increased cybersecurity risks in healthcare facilities.
Clearswift conducted a survey into cybersecurity in healthcare and found that less than a quarter of respondents claimed to have “adequate” levels of budgeting allocated to security. In the same survey, only 26% of respondents said they were investing in endpoint security. This specific statistic is concerning with regards to hardware attacks since endpoints are a key target. Furthermore, this demonstrates that healthcare facilities have a lack of understanding as to what they are vulnerable to. Moreover, an abysmal one out of hundreds of NHS trusts passed the government-backed Cyber Essentials Plus assessment which includes a range of security tests.
Lack of Employee Cybersecurity Training
Without sufficient cybersecurity software in effect, employees stand as the main barrier protecting healthcare facilities from cyberattacks. However, the lack of investments into cybersecurity also applied to employee training on the subject. With a lack of awareness regarding cybersecurity risks and practices, employees are not a reliable form of protection and are often the primary cause of cyberattacks. This is especially dangerous since an increasing number of NHS staff are provided with access to critical systems. This means any error made could have dire consequences. Furthermore, hardware attacks regularly rely on social engineering techniques since the attackers need to acquire physical access to an entity. With employees oblivious to such methods as a result of insufficient training, attackers can successfully manipulate staff and carry out attacks.
Legacy Security Systems in Healthcare
Many systems within the healthcare industry are outdated in terms of cybersecurity. Having been built without cybersecurity in mind, these systems have fewer, to no obstructions to cyber criminals. Many systems also lack two-factor authentication, a basic form of cybersecurity in current times. This further facilitates the attacker’s job.
Increased Reliance on IoT and Connected Medical Devices
All these vulnerabilities are not helped by the fact that the healthcare industry is increasingly relying on technology. More and more medical devices are now part of the IoT. This increases the attack surface for malicious actors since there are more entry points, and more devices storing patient data. Importantly, many of these IoT medical devices perform life-saving operations and/or allow patients to continue their daily lives.
Medical IoT devices include connected inhalers which allow for better management of asthma; automated insulin delivery systems which continuously monitor a patient’s blood glucose without requiring a finger prick test; and implantable pacemakers, to name a few. IoT devices are vulnerable to attacks, and an attack on a medical IoT device can have extremely damaging results.
Furthermore, COVID-19 has resulted in proliferated remote work. The healthcare industry is no exception since some operations can be conducted online. This makes it easier to attack the NHS since it is becoming increasingly reliant on its network. Many devices connecting to it could be employees’ personal devices which have fewer security features in place, thereby increasing the cyber risks.
The Supply Chain poses a Cyber Security Risk
With the increased reliance on technology comes the increased reliance on the supply chain, since devices used in the healthcare industry are manufactured by third parties. The supply chain is a cybersecurity risk due to the inconsistencies in security measures. If an organization is too difficult to infiltrate, malicious actors often turn to the organization’s supply chain. This is due to the fact that there are likely less stringent security measures in place.
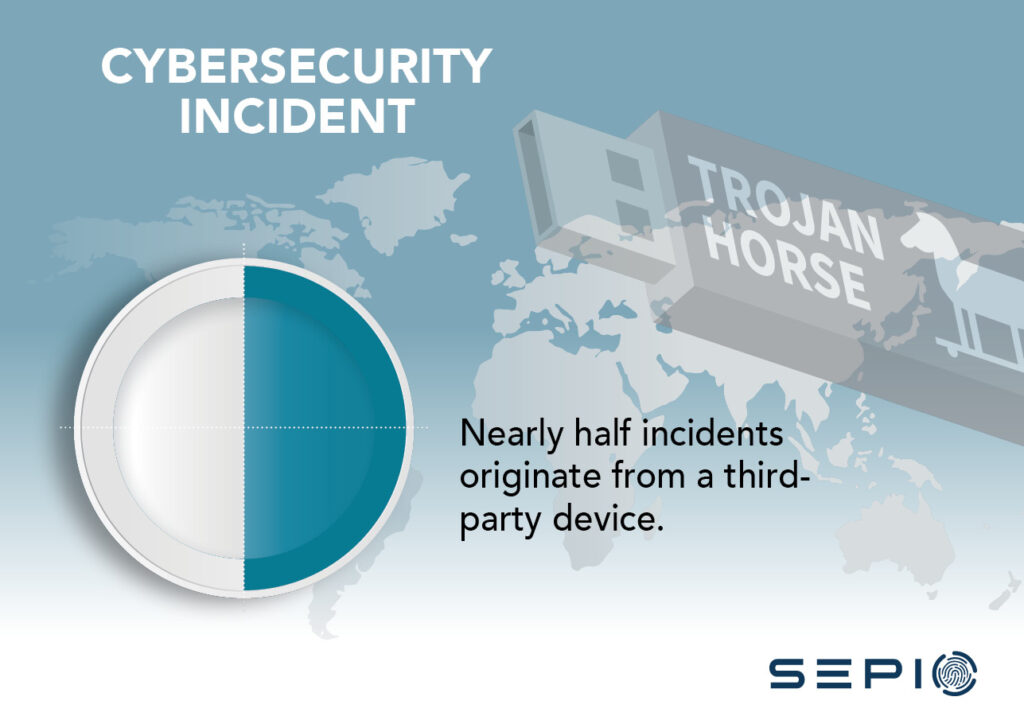
Devices can be manipulated by cyber criminals in the supply chain with the intent of said device being used by the target organization. This is a very real threat, with almost 50% of incidents originating from a third-party device, such as an IoT device or hardware peripheral.
Hardware Attacks are Easier in Public Facilities
Hardware attacks require that the attacker gain physical access to its target. Healthcare entities are relatively easy to gain access to and are often designed with a high level of openness to facilitate operations. However, this openness makes the attacker’s job easier since devices can more easily be tampered with. And, with thousands of people coming in and out of hospitals daily, including patients, doctors, nurses and secretaries, how could one detect the presence of a malicious actor disguised as one of the many genuine individuals that can be found in a hospital?
Are Hospitals Even Safe?
In short, yes. Here at Sepio, we are not discouraging you from going to visit a doctor if you are feeling unwell (it is necessary to emphasize this). However, this blog seeks to highlight the risks of insufficient cybersecurity within the healthcare sector in an effort to improve operations, data confidentiality, and general security within the industry. The healthcare industry’s prioritization of patient care must now come hand-in-hand with cybersecurity. In 2021, the former without the latter is simply an oxymoron.









