Airport Hardware Security Gaps: The Hidden Risk to Operational Resilience
Airport hardware security gaps are emerging as a critical risk to operational resilience as airports evolve into complex cyber-physical environments. As a result, a single compromised device can disrupt operations across terminals, airlines, and passenger services within minutes.
Modern airports depend on thousands of connected hardware assets supporting passenger processing, baggage handling, airside operations, building systems, access control, surveillance, telecom, retail, and third-party services. Consequently, a failure or compromise in any of these domains can quickly escalate into widespread disruption affecting airlines, ground handlers, tenants, and passengers.
Airport cybersecurity must go beyond data protection to ensure operational continuity, resilience, and trust across connected systems.
Despite investments in endpoint security, network monitoring, identity management, OT security, and segmentation, a critical blind spot remains: organizations often cannot verify what a connected device truly is at the physical hardware level.
Traditional methods for identifying connected devices are unreliable:
- MAC addresses can be spoofed
- Hostnames can be misleading
- Certificates do not prove physical identity
- Agents are not universally supported (especially in OT and IoT environments)
- Network visibility is limited by encryption and segmentation
In dynamic airport environments involving airlines, vendors, contractors, and tenants, asset inventories quickly become outdated, leaving critical gaps in visibility and trust.
Airport Cybersecurity: Zero Trust Hardware Access
Sepio’s Zero Trust Hardware Access platform strengthens airport hardware security by closing this visibility gap and extending trust verification to the physical device layer.
Powered by AssetDNA™ technology and physical-layer intelligence, airport organizations can:
- Discover all connected airport assets across IT, OT, and IoT environments
- Verify the true identity of each connected device
- Validate device role, behavior, and physical location
- Continuously assess device risk posture
- Enforce security policies using existing airport workflows
This provides airport security, IT, OT, engineering, and operations teams with a reliable foundation for cyber resilience. Instead of relying solely on what a device claims to be, teams gain visibility into what is connected, whether it is expected, and what actions to take.
The result is a stronger model for airport cyber resilience, one where trust begins at the hardware layer, before network access, software identity, or user activity. In modern airport environments, Zero Trust must start with the Hardware Access.

Airport Security Across IT, OT, and IoT Environments
Airport hardware security is inherently complex due to the mix of IT, OT, IoT, and cyber-physical systems (CPS) that support daily operations. Some systems are managed by the airport authority, while others are operated by airlines, tenants, vendors, and government agencies.
This creates a dynamic environment where systems ownership, location, and trust continuously change and are difficult to verify.
Typical Connected Airport Hardware Assets
- Passenger kiosks and check-in hardware systems
- Baggage handling control equipment and PLCs
- CCTV, surveillance, and access control devices
- Biometric identification and authentication systems
- HVAC and building management systems
- Network infrastructure and endpoints
- Vendor-managed, third-party, and unmanaged hardware assets
Each of these assets expands the airport’s attack surface. When hardware identity and visibility are limited, all higher-level security controls inherit risk, weakening overall airport cyber resilience.
The Expanding Airport Cyber Attack Surface
Today, airport cybersecurity is no longer just about data protection, it is about maintaining operational resilience across an increasingly hardware-driven attack surface. As a result, a cyber incident involving connected devices can disrupt check-in, baggage handling, passenger communications, access control, and incident response.
Even so, without impacting critical safety systems, these disruptions can still lead to delays, manual workarounds, reduced efficiency, and reputational damage.
Key factors expanding the attack surface include:
- Converged IT/OT environments: Corporate, terminal, and operational systems often share dependencies, even when segmented
- Vendor and tenant ecosystems: Third-party devices reduce hardware visibility and ownership clarity
- Unmanaged and agentless assets: Legacy, IoT, and externally managed devices limit security control
- Physical access realities: Distributed environments make device enforcement more difficult
- Digital transformation in airports is driving growth in connected technologies while expanding the cyber attack surface.
Why Zero Trust Falls Short Without Hardware Verification
Zero Trust has transformed cybersecurity by requiring explicit verification of users, applications, and access (NIST SP 800-207). However, most implementations rely on the software or identity layer, assuming devices are what they claim to be.
In airport environments, devices may be:
- Unknown or unmanaged hardware assets
- Misclassified, repurposed, or undocumented devices
- Spoofed, impersonated, or compromised endpoints
- Connected outside approved network zones or physical locations
Why Software Identity Is Not Enough
- Network identifiers (MAC, IP) do not prove physical hardware identity
- Security agents cannot be deployed across all OT, IoT, and legacy systems
- Network traffic inspection is constrained by encryption and segmentation
- CMDB and asset inventory data quickly become outdated
- Vendor-provided equipment requires independent validation
Without hardware-level verification, Zero Trust relies on assumptions rather than evidence, introducing risk where device identity cannot be guaranteed.
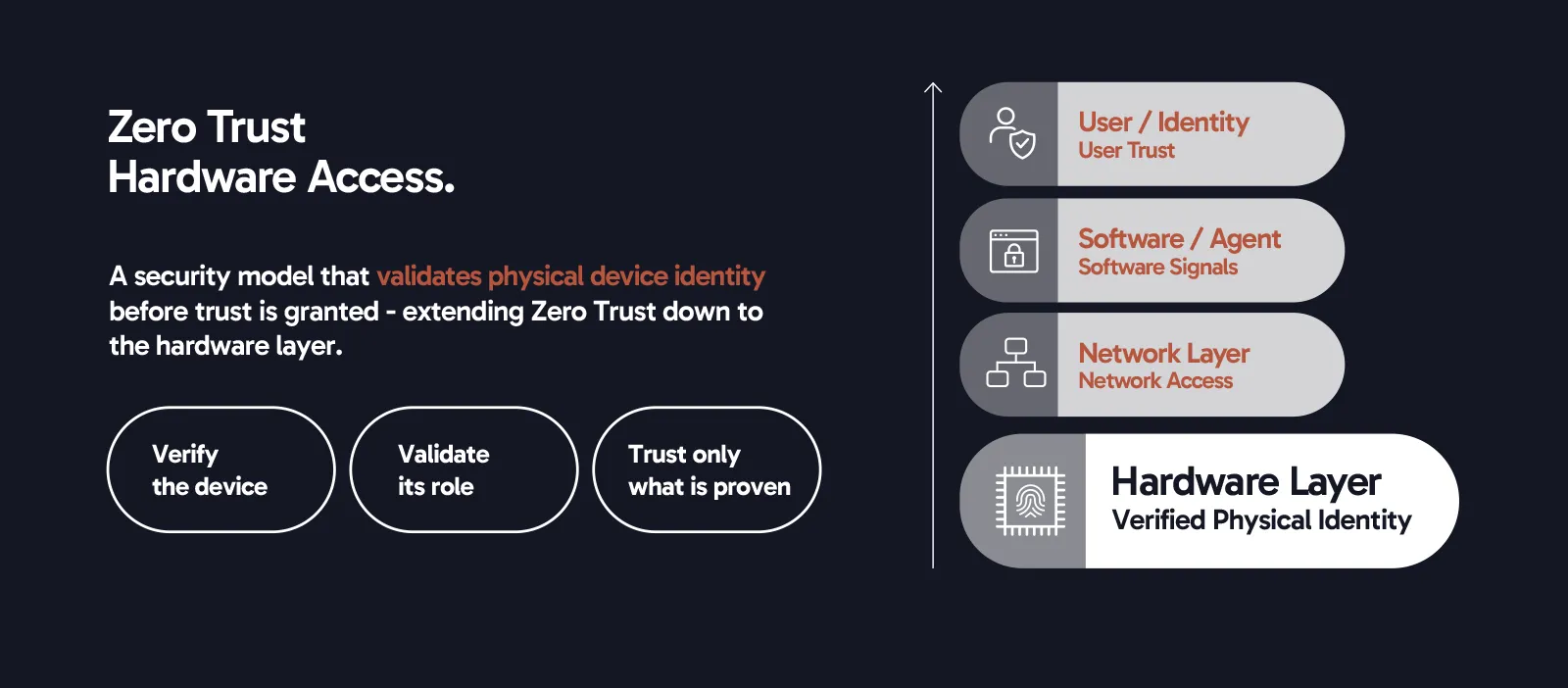
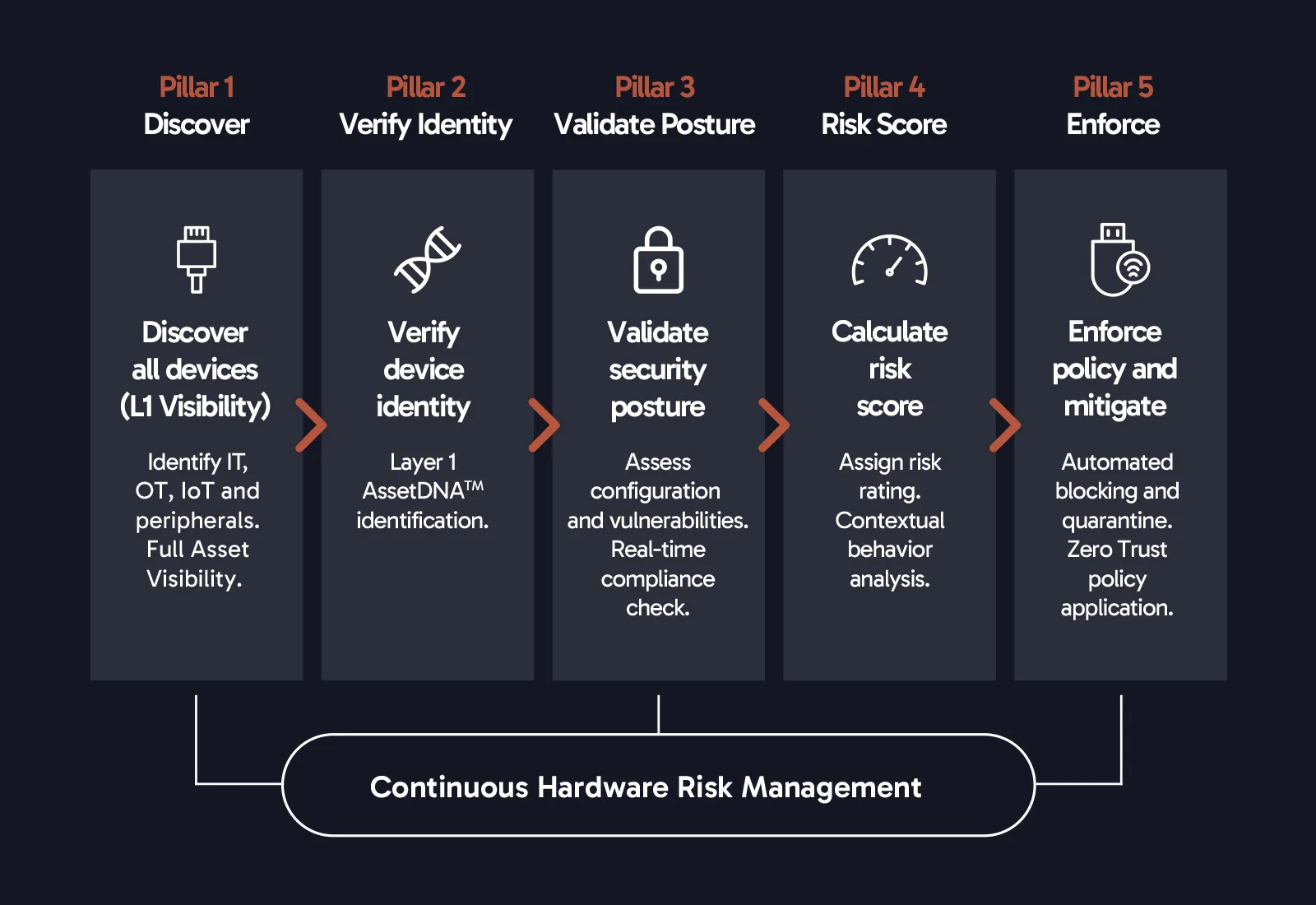
The Zero Trust Hardware Framework for Airport Security
To address these challenges, a complete airport hardware security strategy requires a Zero Trust framework built on five core pillars:
Discover: Continuously identify all connected hardware across IT, OT, and IoT.
Verify: Establish true identity using physical-layer intelligence.
Validate: Confirm alignment with expected role, location, and ownership.
Score: Assess risk based on exposure, context, and trust.
Enforce: Trigger actions through policies, alerts, and integrations.
Together, these pillars provide a comprehensive approach to airport hardware security. By continuously validating device identity and behavior, organizations can reduce blind spots, strengthen Zero Trust implementation, and improve overall cyber resilience.
Key Airport Security Use Cases
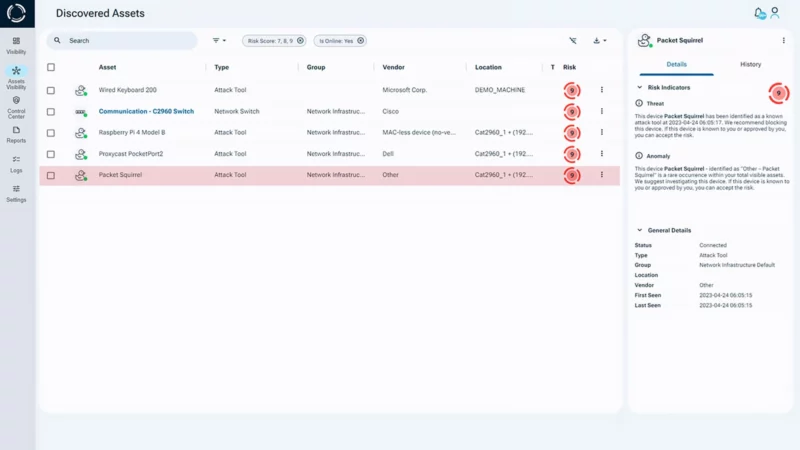
Airport environments require continuous visibility and control over connected hardware assets across IT, OT, and IoT systems. Accordingly, key use cases include:
Unknown and Unmanaged Asset Discovery: Identify unknown, unmanaged, and shadow hardware devices across airport networks to eliminate visibility gaps.
Rogue Device Detection: Detect unauthorized or malicious hardware devices in operational zones, restricted areas, and critical infrastructure environments.
OT and Infrastructure Visibility: Gain deep visibility into operational technology, including baggage handling systems, HVAC, and building infrastructure.
Endpoint Coverage Gaps: Identify hardware devices that lack endpoint protection (EDR), network access control (NAC), or monitoring capabilities.
Third-Party Device Governance: Validate, monitor, and control hardware assets introduced by airlines, vendors, contractors, and tenants.
Incident Response Acceleration: Quickly identify affected hardware assets during security incidents to enable faster, more accurate response.
Supporting Airport Cybersecurity Objectives
Airport cybersecurity programs focus on visibility, control, and compliance. To support this, Sepio adds hardware-level visibility, device identity verification, and continuous validation.
Asset Discovery: Maintain a complete, up-to-date inventory of IT, OT, IoT, and cyber-physical assets. Sepio continuously discovers and classifies connected hardware devices.
Segmentation Readiness: Ensure devices are placed in the correct network zones and detect policy violations. Sepio validates device identity and location against segmentation policies.
Access Control: In addition, prevent unauthorized device access to critical systems. Sepio enables trust-based enforcement, including allow, block, quarantine, and escalation actions.
Continuous Monitoring: At the same time, detect changes that may impact operations. Sepio provides continuous visibility into device identity, behavior, and connectivity.
Risk-Based Remediation: Furthermore, prioritize response based on real risk and asset criticality. Sepio enhances risk scoring using hardware identity, location, and context.
Audit Evidence: Finally, demonstrate control over connected assets. Sepio delivers validated hardware-level records and detailed audit history.
The Future of Airport Cybersecurity Depends on Trusted Device Identity
Airports are becoming more connected and automated, increasing reliance on devices that must be trusted.
Traditional controls, visibility, endpoint security, network monitoring, and access control, remain essential. However, without verified device identity, security decisions are still based on incomplete data.
To address this, Sepio’s Zero Trust Hardware Access (ZTHA) approach extends Zero Trust to the physical layer, enabling airports to discover, verify, and enforce trust in every connected device across IT, OT, and IoT environments.
Ready to eliminate hardware blind spots in your airport environment? Schedule a demo.
Download the Zero Trust Hardware Access for Airports (pdf)





