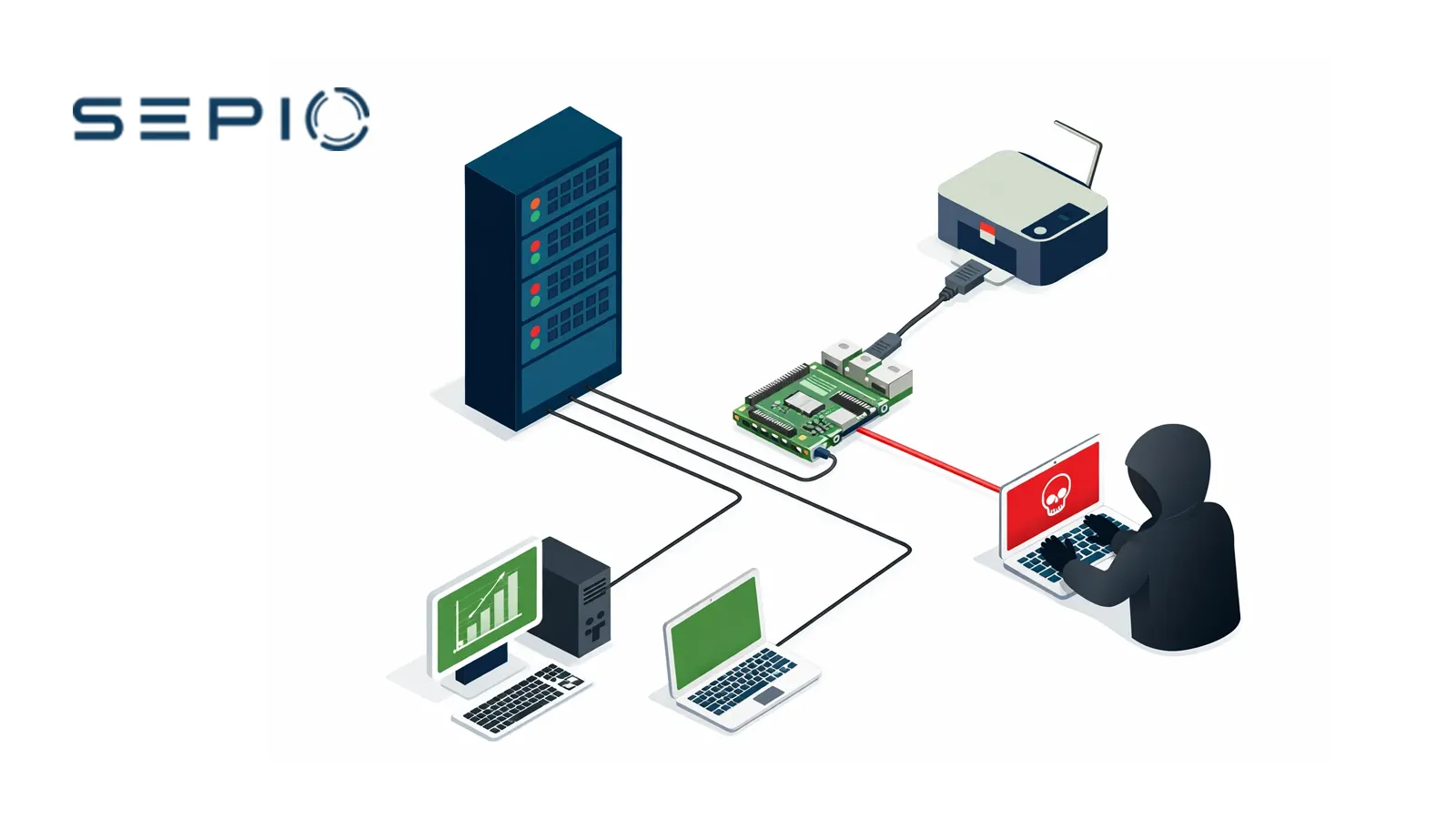
Printer Man‑in‑the‑Middle Use Case
Rogue hardware detection has become increasingly critical for financial institutions as attack techniques shift from software exploitation to hardware‑based intrusion methods. Printers, multifunction devices, and other embedded systems are particularly attractive targets because they are widely trusted, rarely monitored at the physical layer, and often unmanaged by endpoint security controls.
Unlike traditional malware attacks, rogue hardware devices require no credentials, malware installation, or remote exploitation. Once physically inserted, these devices can silently intercept data, alter traffic, or provide persistent access paths that bypass network segmentation and authentication mechanisms entirely. Without effective rogue hardware detection, financial institutions may remain unaware of such threats for months or longer.
Why Printers Are a High‑Risk Vector
Network printers challenge Zero Trust enforcement because organizations treat them as benign, mission‑critical systems that must stay online at all times. Security teams therefore exclude printers from agents, strict monitoring, and access enforcement.
Hackers exploit this implicit trust by inserting inline hardware implants that impersonate legitimate printer connections. These rogue devices inherit the printer’s trust level while enabling man‑in‑the‑middle (MITM) access to sensitive financial records, transaction logs, and regulated customer data.
Traditional monitoring tools may see only normal printer traffic, while the rogue device operates invisibly below the visibility of software and network‑centric defenses.
Rogue Hardware Detection Use Case
Industry: Financial Services Institution.
Rogue Device Detection Scenario: An hacker inserts a rogue hardware implant inline with a trusted network printer. The implant creates a hidden man‑in‑the‑middle (MITM) path while the printer continues to function normally. This normal operation conceals the attacker’s presence.
Hardware Attack Tool: The hacker deploys a Raspberry Pi–based transparent bridge that impersonates a legitimate printer connection. The device intercepts print traffic and exfiltrates data over an unauthorized wireless channel, while users and IT teams see no operational disruption.
Exposure Window: The rogue hardware device operates passively and mimics a legitimate hardware path. As a result, it evades traditional MAC‑based controls, traffic analysis, and software security tools. This allows the hardware device to remain undetected for extended periods.
Challenge: Organizations struggle to enforce Zero Trust when they assume hardware identity instead of verifying it. Printers, IoT devices, and OT‑connected assets often lack physical‑layer inspection, allowing attackers to operate below software and network visibility.
Risk: The environment continues to trust the connection because the device appears legitimate. This enables policy bypass, sensitive data exposure, and persistent hardware‑level access, creating a hidden foothold inside a regulated financial environment.
The Sepio Solution
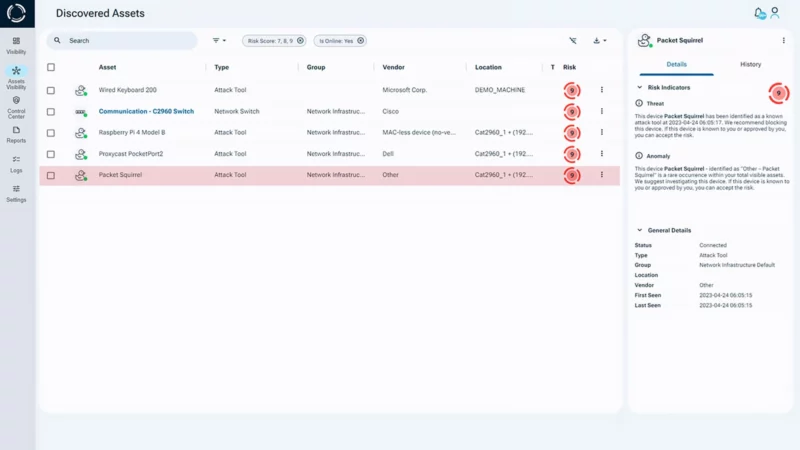
Sepio enforces Zero Trust Hardware Access (ZTHA) by delivering rogue hardware device detection at the physical layer. The platform verifies the true hardware identity of every connected device and exposes rogue or manipulated assets, even when they imitate trusted equipment.
Security teams gain the ability to:
- See what is actually connected
- Detect rogue and impersonating hardware
- Apply policy based on verified hardware identity
- Reduce risk from stealth, hardware‑based attacks
Why Rogue Hardware Detection Matters for Zero Trust
Zero Trust fails without visibility into what physically connects to the environment.
Rogue and impersonating devices can inherit trust when security controls rely solely on declared identity, MAC addresses, traffic behavior, or software agents. Many hardware threats exist below the visibility of traditional defenses, including unmanaged, embedded, MAC‑less, and manipulated devices.
Recent 2025 NIST research confirms that hardware is frequently susceptible to design and implementation weaknesses that evade traditional security controls and enable persistent risk below software and network visibility.
Rogue Hardware Detection at the Physical Layer
Modern enterprises need more than asset inventory, they need trustworthy hardware identity.
Across IT, OT, IoT, and hybrid environments, hidden and spoofed devices introduce blind spots that undermine segmentation, compliance, and incident response. Sepio closes this gap by delivering verified hardware visibility across network, USB, and peripheral interfaces.
In as little as 24 hours, Sepio reveals hidden hardware exposure across the environment. The platform verifies the true identity of connected devices and helps organizations strengthen Zero Trust enforcement at the physical layer.
Zero Trust Hardware Access Benefits
Verified Hardware Visibility
Discover connected assets across IT, OT, IoT, and peripherals based on their true physical identity, not just what they claim to be, exposing hidden, unmanaged, and impersonating devices.
Policy Enforcement Based on Trusted Identity
Apply security policies using verified hardware context. This approach supports compliance, reduces operational friction, and enables Zero Trust without requiring a perfectly clean starting point.
Faster Mitigation of Rogue Devices
Once rogue or suspicious hardware is detected, teams can trigger response workflows through existing enforcement and orchestration tools to contain risk faster.
Why Existing Security Leaves a Hardware Blind Spot
Most security controls focus on software, traffic, or declared network identity. Sepio adds the missing hardware truth layer, helping organizations detect rogue devices and verify identity where trust begins.
Why Sepio for Rogue Hardware Detection
Organizations use Sepio to implement Zero Trust Hardware Access (ZTHA) by verifying the true identity of every connected hardware asset. With this approach, security teams gain visibility into hidden, rogue, unmanaged, and impersonating devices across enterprise, industrial, and hybrid environments. This verified hardware insight enables stronger policy enforcement and meaningful risk reduction at the physical layer.
Sepio, See What You’ve Been Missing™

Ready to Strengthen Rogue Device Detection?
Rogue hardware threats operate below the visibility of traditional security controls. See how Rogue Device Detection and Zero Trust Hardware Access (ZTHA) can help you expose hidden devices, verify true hardware identity, and reduce physical‑layer risk in your environment.
Discover what’s really connected to your environment. Talk to an expert.
Download the Printer MITM Use Case








