A Man in the middle attack (MiTM) occurs when a hacker intercepts and manipulates communication between two parties. This type of attack allows the hacker to secretly monitor, tamper with, or inject malicious data into the communication, compromising the integrity and confidentiality of the exchange. By positioning themselves within the network pathway, the attacker can eavesdrop on messages, alter content, or introduce fraudulent data without being detected.
A MiTM attack can serve various malicious purposes, such as stealing sensitive information like login credentials, financial data, or personal details. Attackers may also use this method to inject malware into the communication stream or impersonate one of the parties to gain unauthorized access to systems or services. These attacks are often combined with phishing schemes and other forms of social engineering to exploit unsuspecting victims.
What is a Man in the Middle Attack?
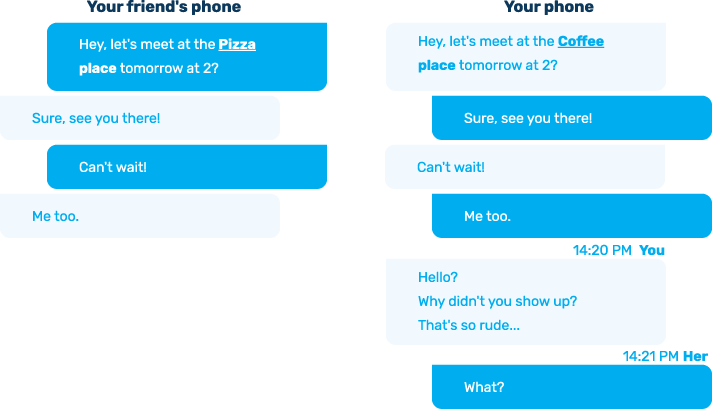
Imagine you’re texting a friend to arrange a meetup. She suggests meeting at 2 pm at your local coffee shop. You arrive on time, but she’s nowhere to be found. Meanwhile, your friend is sitting at your favorite Italian restaurant, wondering why you didn’t show up. What happened?
Without your knowledge, a hacker intercepted your messages, read them, and altered the details without either of you noticing. This is a classic example of a Man in the Middle attack (MiTM).
While the scenario above might seem harmless, a Man in the Middle attack is far more dangerous in real-world applications. Hackers aren’t typically interested in disrupting casual meetups between friends. Instead, they use this technique to target organizations, businesses, or specific individuals to steal sensitive information, manipulate data, or gain unauthorized access to systems.
How a Man in the Middle Attack Works
In a MiTM attack, the attacker secretly positions themselves between two communicating parties, such as a user and a website or two endpoints on a network. By doing so, they can intercept, monitor, and even manipulate the communication without either party realizing it. Here’s a breakdown of how this type of attack typically unfolds:
Breaking Down the Stages of an Attack
- Interception: The attacker first intercepts the communication between the two parties, making them believe they are communicating directly with each other. This can be achieved through various methods, such as exploiting vulnerabilities in network protocols or using spoofing techniques, or setting up rogue Wi-Fi hotspots.
- Eavesdropping: Once the attacker has positioned themselves in the middle, they can eavesdrop on the data being transmitted. This allows them to collect sensitive information, such as login credentials, credit card numbers, or other confidential details.
- Modification: The attacker can alter the data being transmitted. For example, they might modify a legitimate message, redirect a user to a malicious website, or inject malware into the communication.
- Impersonation: The attacker can impersonate one or both parties involved in the communication. This allows them to gain unauthorized access to systems or manipulate the communication for their benefit.
These techniques allow a threat actor to compromise confidentiality, integrity, and authenticity, the core pillars of secure communication.
Man in the Middle Hardware Attack Tools
While some MiTM attacks exploit software vulnerabilities or network weaknesses, others rely on physical hardware implants that intercept traffic at the device or port level. These hardware-based attacks are especially dangerous because they often operate below the visibility of traditional security tools.
Below are common categories of hardware used in real-world MiTM campaigns, explained for awareness and defensive preparedness.
Internal Implants in ATMs and Payment Systems
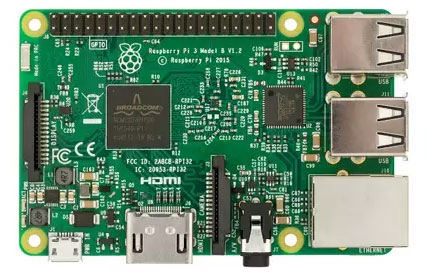
ATMs are prime targets for man-in-the-middle attacks due to the abundance of cash stored inside them. One way such an attack can be executed is through a black box attack. In this method, a MiTM attack tool, often a Raspberry Pi Zero W, is connected between the ATM’s PC and the dispenser. This setup allows the attacker to send cash-dispensing commands to the machine.
This type of MiTM attack can be challenging because it requires internal access to the machine. However, a simpler method is available for just $25 on Amazon. No need for the dark web when it comes to this. This Man-in-the-Middle attack tool, known as a GL.iNet, attaches externally to the ATM but produces the same end result.

ATMs may be a niche target, but you could be at risk too. Hackers don’t care about your lunch plans; they target access to the organization you work for. They could use you as a gateway, employing social engineering techniques to exploit your trust and gain entry.
At this point, you might think you’re protected, especially since accessing your organization’s network assets and network likely requires authentication, perhaps even biometric authentication. However, another man-in-the-middle attack tool is capable of bypassing this as well. A Man in The Middle unit known as the BeagleBone board can circumvent even the most sophisticated biometric authentication methods, such as palm-vein scanners.

Hak5 MiTM Hardware Attack Tools
There are plenty more tools that can be used for a MiTM attack. Hak5 is a company that produces a lot of these man in the middle attack tools, such as Packet Squirrel, WiFi Pineapple, LAN Turtle, and others. These devices, although differing slightly in functionality, both observe network traffic. WiFi Pineapple, a powerful MiTM tool, allows hackers to mimic trusted networks, collect data, and facilitate cybercrime.

How Attackers Bypass Security Defenses
Man in the middle attack tools can bypass existing security solutions, such as Network Access Control (NAC), Intrusion Detection System (IDS), and IoT network security, due to a lack of physical layer visibility, allowing them to remain undetected. To mitigate MiTM attack tools, it is critical to prevent the use of rogue hardware tools. This awareness is increasingly important as hardware-based attacks become more common. In 2020, 37% of threats targeted USB exploitation. This is nearly twice the percentage recorded in 2019. Additionally, with USB usage increasing by 30% in 2020, attackers have a greater likelihood of success.
MiTM Attack Mitigation
MiTM attack mitigation requires organizations to implement comprehensive cybersecurity solutions. Sepio’s patented technology offers an effective solution for mitigating the risks posed by MiTM attack tools. The prevalence and sophistication of man-in-the-middle attack highlight the need for proactive defense strategies. By understanding attackers’ tactics and maintaining vigilance, organizations can safeguard their networks and sensitive data from compromise.
How to Detect a Man in the Middle Attack
Sepio is calculating the individual risk score of all network assets. Through a comprehensive analysis of multiple, different risk indicators, each of which contributes a different level of risk to the final score. You can categorize these risk indicators into the following groups, listed in order of increasing severity from low to high:
- Unsupervised assets: Assets that are not actively monitored on the network.
- Asset anomalies: Devices exhibiting unusual behavior, such as Asset DNA mismatch or unexpected ports (for example, physical layer based mismatch, rare devices, unexpected devices or components, unexpected port speed, etc.).
- Known vulnerabilities: Assets with known CVE vulnerabilities (device CVE and / or firmware CVE, and / or component CVE).
- Known attack tools: Devices matching known hacking tools (based on Sepio’s Asset DNA match), such as man-in-the-middle attack tools.
By leveraging these indicators, Sepio helps identify rogue devices within the network and detect Man-in-the-Middle attacks, ensuring the integrity of your computer networks.
Prevent a Man in the Middle Attack
Man-in-the-middle attack tools pose a serious cybersecurity threat, allowing attackers to intercept and alter communications. These attacks can steal sensitive data, weaken security, and enable unauthorized changes. To prevent them, organizations must understand attacker tactics and implement strong defenses.
Sepio’s platform offers a powerful defense against Man in the Middle attack by providing comprehensive visibility and security across network assets. By prioritizing hardware-based security, organizations can effectively safeguard their networks, ensuring they are resilient to evolving cyber threats.
See Every Asset. Secure Your Network
Schedule a demo today and discover how Sepio’s platform can help you mitigate risks from Man in the Middle attack tools. Let our experts show you how to regain control of your network and ensure resilient security against advanced threats.






