Deeper visibility. Fewer blind spots. Lower risk. Verified trust.
Master the unseen and navigate the growing complexity of connected assets, whether known or rogue, at scale.
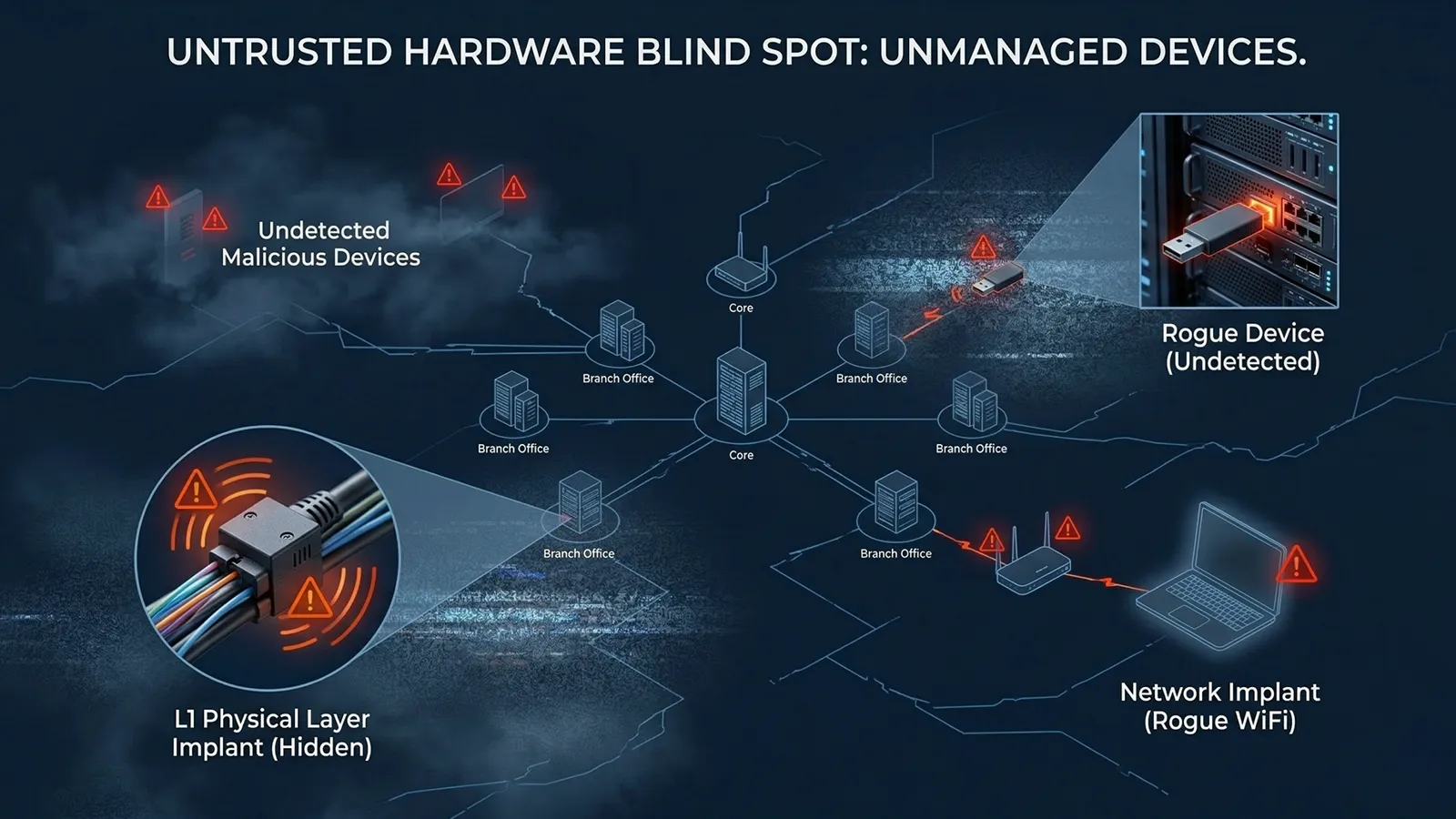
Most Zero Trust strategies verify users, applications, and sessions, but still assume the device itself is legitimate. In financial environments, that assumption creates a dangerous blind spot. Unmanaged peripherals, rogue devices, spoofed assets, network implants, and hidden hardware can persist inside branches, offices, data centers, and ATM environments without being properly identified.
Financial institutions operate highly distributed, fast-changing environments shaped by branch infrastructure, third-party devices, remote work, BYOD, and operational technology. When hardware identity is assumed rather than verified, security teams can miss critical assets and expose the organization to compliance violations, service disruption, fraud risk, and reputational damage.
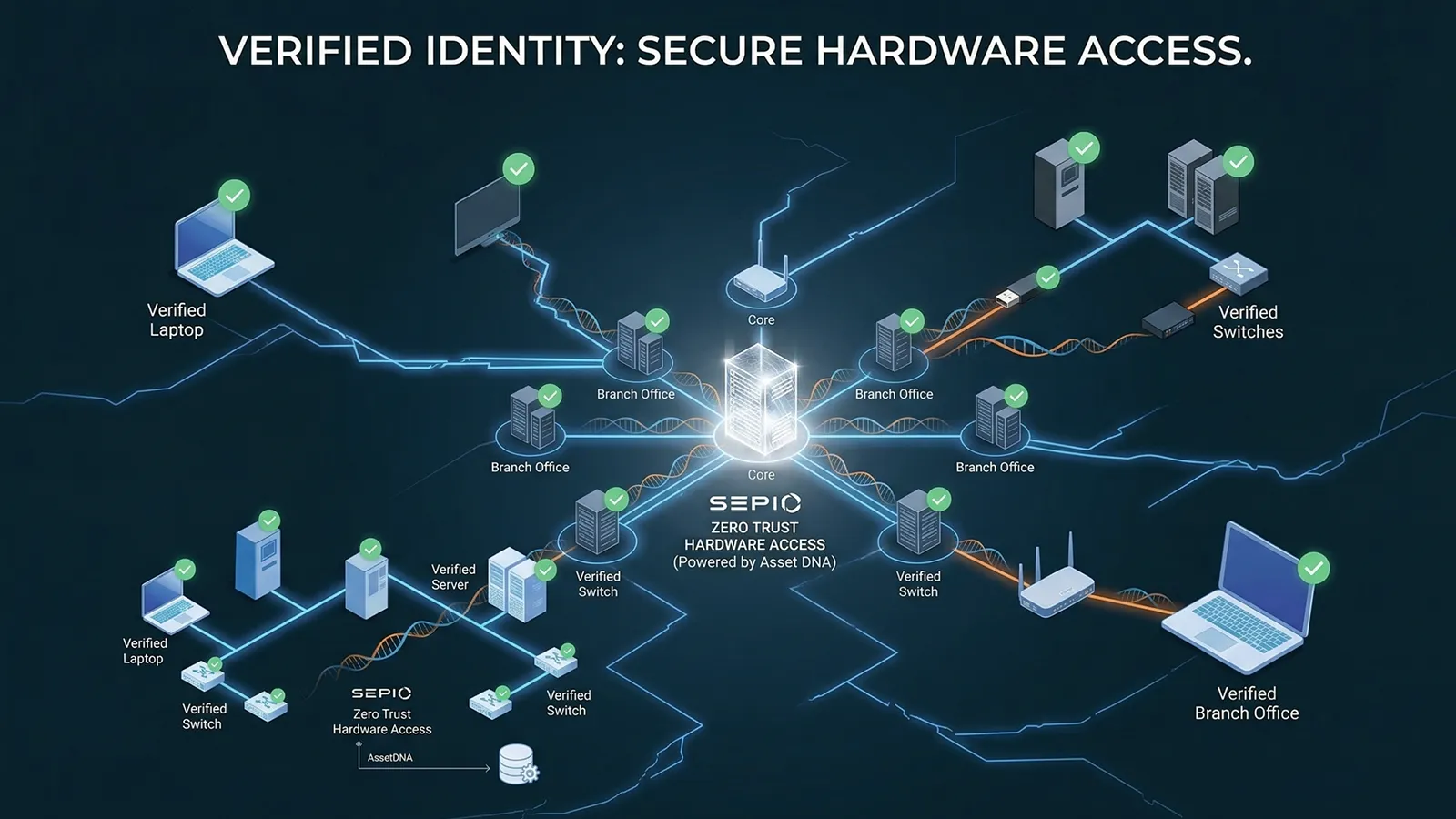
Sepio helps financial institutions close that blind spot with Zero Trust Hardware Access. By using patented physical-layer intelligence, Sepio discovers connected assets, validates their true identity, and establishes trust at the hardware level. This gives security teams accurate visibility into both known and unknown devices without relying on traffic monitoring alone.
With Sepio, financial organizations can strengthen their Zero Trust architecture by bringing hardware into the trust equation—so access decisions are based not only on who is connecting, but also on what is actually connected.
Stop Hardware-Borne Threats
Detect rogue devices, hidden implants, USB spoofing, and man-in-the-middle hardware before they can be used against your environment.
See Every Connected Asset
Gain accurate visibility into known, unknown, managed, unmanaged, and hidden devices across branches, offices, ATMs, and data centers.
Enforce Trust Before Access
Validate hardware identity and apply policy based on what a device truly is, not just what it claims to be.
Support Audit and Compliance Readiness
Strengthen asset accountability, improve evidence collection, and support regulatory and internal control requirements with accurate hardware intelligence.
Reduce Waste and Improve Planning
Identify unused, unmanaged, duplicate, and unnecessary hardware so teams can optimize spend and make better infrastructure decisions.
Close Hardware Trust Gaps
Complement NAC and other security controls with physical-layer asset intelligence that reveals what traditional tools can miss.

To maintain control in modern financial environments, organizations need visibility that goes beyond declared identity and network traffic. They need the ability to see every connected asset—whether on the network, attached locally, or hidden behind spoofed characteristics—and determine whether it can be trusted.
Sepio’s Zero Trust Hardware Access approach uses Physical Layer, data to deliver accurate asset visibility and hardware-level validation across enterprise, branch, and ATM environments. This enables security teams to discover unmanaged and rogue assets, understand where they are connected, and enforce policy based on hardware truth.
Instead of treating every device as trustworthy until proven otherwise, Sepio enables financial institutions to continuously verify hardware identity and prioritize the assets that pose the greatest operational and cyber risk.
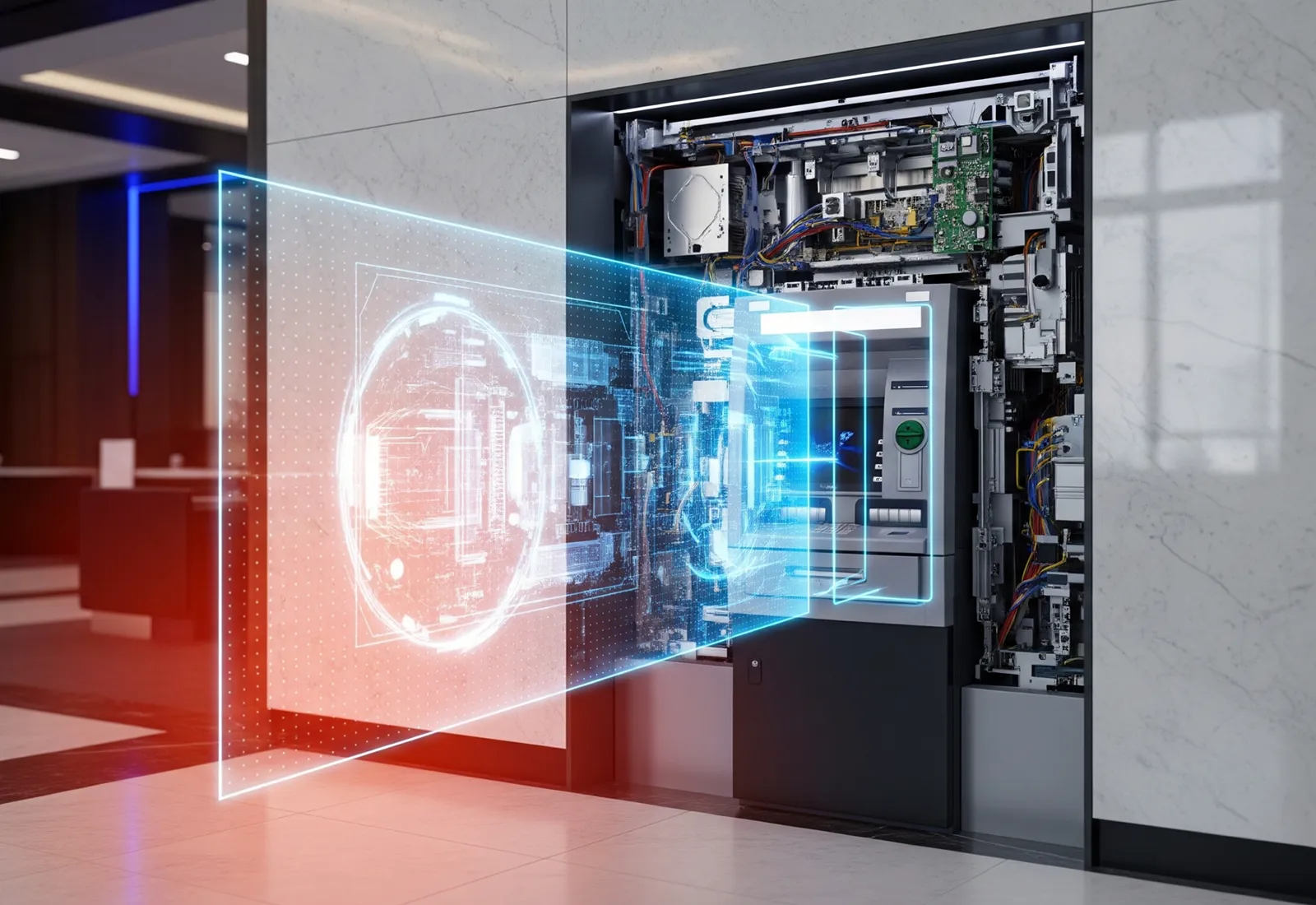
ATMs remain a prime target for hardware-based attacks, including black box attacks and man-in-the-middle techniques that can be executed quickly and often evade traditional security controls. These attacks commonly rely on unauthorized physical devices or hidden hardware implants that are not properly identified by conventional network security tools.
Because many of these attack components do not present a normal network identity, they can remain invisible to solutions that depend on Layer 2 visibility, traffic inspection, or standard endpoint controls. This is exactly where Zero Trust Hardware Access becomes essential.
Sepio enables ATM operators and financial institutions to detect unauthorized hardware at the physical layer, validate device identity, and establish trust before hidden devices can be used to manipulate operations. Sepio’s field-proven ATM deployments help financial organizations reduce exposure to hardware-based fraud, improve operational resilience, and extend Zero Trust principles to one of the most targeted parts of their infrastructure.

Zero Trust Hardware Access helps banks and financial institutions verify the identity and trustworthiness of connected hardware before it becomes a blind spot. It extends zero trust down to the physical layer, where rogue devices, spoofed peripherals, and unauthorized network implants can otherwise go unseen.
Financial environments are dense with ATMs, branch systems, endpoints, peripherals, and third-party devices. When security teams cannot see every connected asset, they inherit unnecessary exposure, including operational disruption, compliance risk, and hidden attack paths.
Yes. Sepio is designed to identify known, unknown, unmanaged, and manipulated hardware assets across distributed financial environments. That includes devices traditional tools may miss, such as network implants, spoofed USB devices, and unauthorized connections.
By building a trusted hardware inventory and exposing hidden assets, Sepio helps financial institutions strengthen control validation, reduce asset-related uncertainty, and support internal risk, audit, and regulatory initiatives.
No. Sepio complements existing tools by adding hardware truth and physical-layer evidence they typically lack. This helps financial institutions close visibility gaps and make existing controls more effective.