Unmanaged and unknown assets create critical security blind spots. Sepio reveals every connected device across your network and endpoints, transforming asset visibility into actionable risk control.
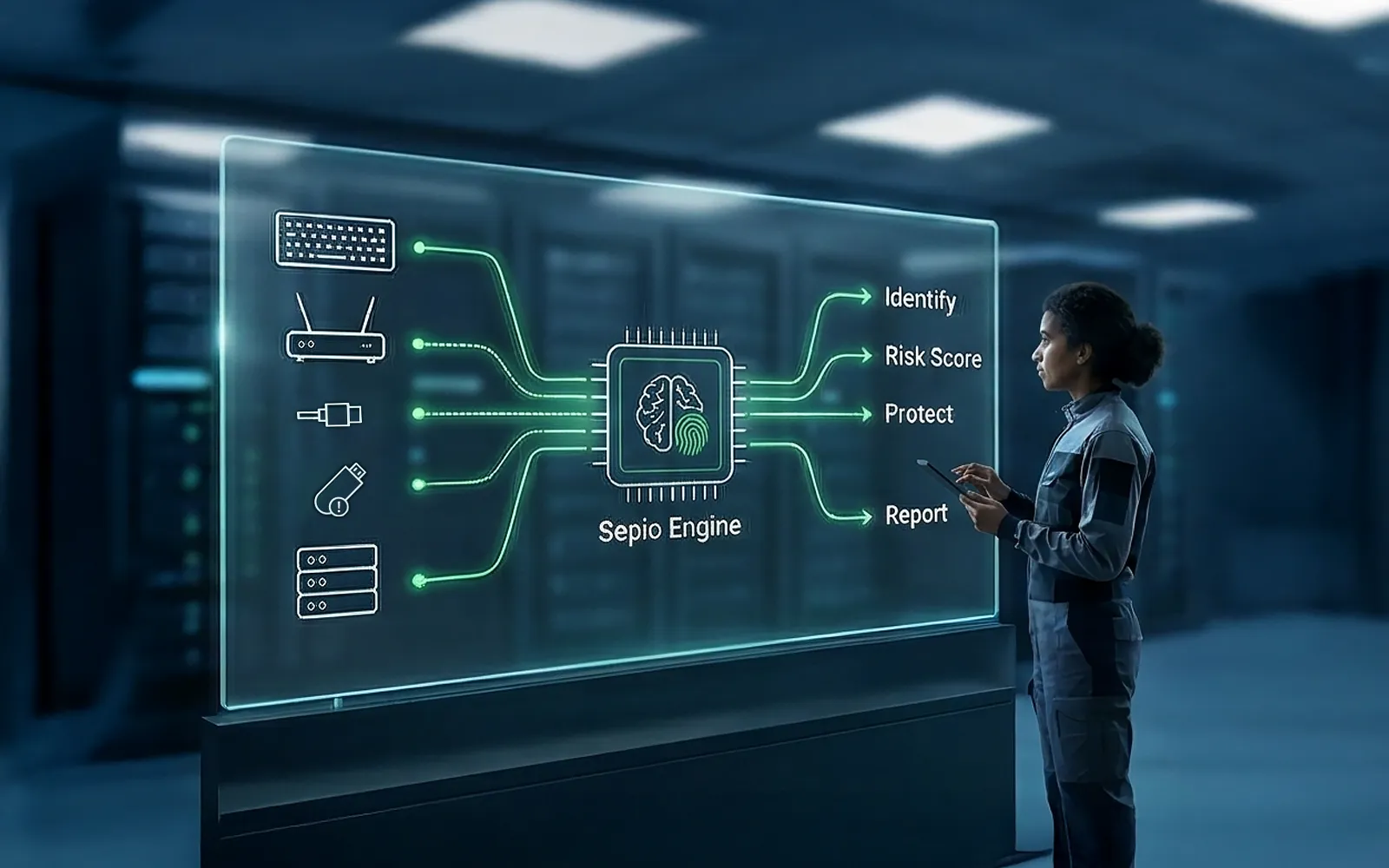
Establish a trusted asset inventory scaled across your network and endpoints down to their peripherals.
As a SaaS or on-prem solution, Sepio’s AssetDNA™ provides field-proven, unparalleled visibility of your IT, OT, and IoT assets in a single pane of view so you can better understand your complex asset ecosystem. By leveraging physical-layer intelligence, Sepio reveals the true identity of every asset, eliminating blind spots caused by unknown, unmanaged, or spoofed devices.
With continuous discovery and validation, security teams gain a complete and accurate understanding of their asset ecosystem, transforming visibility into actionable risk management.
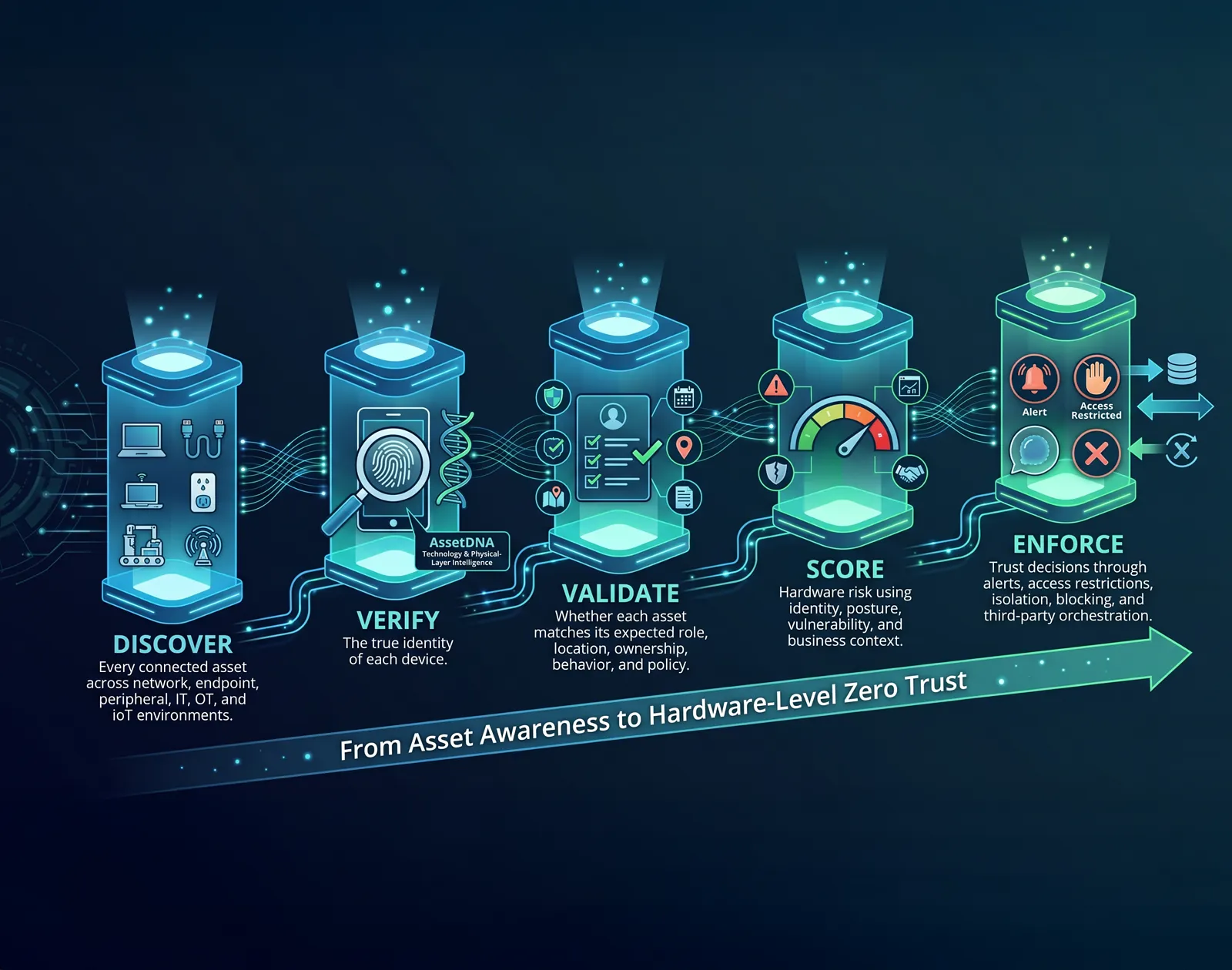
Zero Trust Hardware Access gives organizations a practical framework for extending Zero Trust to the hardware layer. Sepio enables this framework through five connected pillars: discovery, verification, validation, risk scoring, and enforcement.
Discover: Every connected asset across network, endpoint, peripheral, IT, OT, and IoT environments.
Verify: The true identity of each device using Sepio’s patented AssetDNA™ technology and physical-layer intelligence.
Validate: Whether each asset matches its expected role, location, ownership, behavior, and policy.
Score: Hardware risk using identity, posture, vulnerability, and business context.
Enforce: Trust decisions through alerts, access restrictions, isolation, blocking, and third-party orchestration.
Together, these pillars help organizations move from asset awareness to hardware-level Zero Trust – ensuring that every device is verified before it is trusted.
AssetDNA™ is Sepio’s patented method for identifying hardware assets based on their inherent physical characteristics rather than on data that can be changed, spoofed, or hidden. It creates a hardware-level identity for each device, allowing organizations to verify what a device truly is-not just what it claims to be.
By analyzing physical-layer attributes, AssetDNA™ helps uncover rogue, impersonating, unauthorized, and unmanaged devices across the environment. This gives security teams a more trustworthy foundation for visibility, risk assessment, and policy enforcement.
Unlike approaches that rely only on MAC addresses, VID/PID or traffic analysis, AssetDNA™ is built to reveal the real identity of connected assets-even in complex environments where traditional tools can be misled.

Sepio correlates discovered assets with external vulnerability sources, OSINT, and internal cyber research to help identify devices that may be exposed, outdated, unsupported, or associated with known hardware, firmware, or vendor-related risk.
Because Sepio maps this intelligence to verified hardware identities, security teams can prioritize remediation based on what the asset truly is, where it is connected, and whether it aligns with policy.
The result is more accurate risk scoring, less manual investigation, and faster action on the hardware risks that matter most.

Enable action at scale to regain control of your dynamic asset risk surface.
Sepio transforms visibility into action through automated, policy-driven enforcement. Based on asset identity, risk posture, and organizational policies, actions can be triggered instantly, without the delays and inconsistencies of manual intervention.
Security teams can automatically isolate, block, alert, or restrict devices in real time, ensuring threats are contained before they can spread. Integration with third-party security and IT tools further extends enforcement capabilities, enabling seamless orchestration across your existing ecosystem.
Complete Visibility of Assets
Complete visibility to all of your assets – whether connected as a peripheral or a network element.
Uncontrolled Asset Mitigation
Mitigate risks from uncontrolled or spoofing assets.
Low Cost of Ownership
Easy to operate, requiring low maintenance and minimal human intervention.
Asset Policy Enforcement
Enforce specific asset usage – creating granular access control based on regulatory compliance, roles or asset characteristics.
Actionable Measures
No complicated rules or post-processing required. Required measures are clearly delivered to the user.
Native 3rd Party Integrations
Out-of-the-box integration with leading cybersecurity products.
Sepio turns broad asset visibility into verified hardware trust. With continuous validation of every connected asset’s true identity, teams can detect rogue and spoofed devices faster, focus on the risks that matter most, and strengthen security with confidence.
Zero Trust Hardware Access extends the Zero Trust principle of “never trust, always verify” to the hardware layer. It requires organizations to verify what a device truly is before allowing it to connect, communicate, or operate in the environment.
Traditional Zero Trust programs often verify users, applications, and sessions, but still assume device identity based on identifiers that can be spoofed or misrepresented. ZTHA addresses that gap by validating the hardware itself.
ZTHA is designed to reduce hardware blind spots, including shadow IT, spoofed assets, dormant implants, rogue devices, and dual-use devices that can evade network-centric controls.
AI is accelerating vulnerability discovery and lowering the barrier to exploitation, while fragmented security tools continue to create blind spots across IT, OT, and IoT environments.
Traditional Zero Trust focuses heavily on users, apps, and access decisions. ZTHA extends that model to the physical layer, ensuring that trust is not granted to a device simply because it appears legitimate.
There are three guiding principles: never trust, always verify; verify explicitly; and assume breach. These principles are applied to hardware as well as to users and workloads.
The framework is organized into five layers: Visibility, Identification, Policy & Posture, Risk Score, and Control & Enforcement. Together, they move an organization from asset awareness to real-time policy enforcement.
It means access decisions should rely on continuously evaluated signals such as identity, location, device health, behavior, and policy context rather than one-time trust assumptions.
It requires comprehensive asset discovery and mapping of all connected devices, including IT, IoT, OT, shadow IT, USB devices, unmanaged assets, and devices that may be invisible to network-centric tools.
Because simply knowing a device is present does not prove its identity, policy alignment, or risk level. ZTHA builds from visibility into verification, compliance validation, prioritization, and enforcement.
This layer establishes device identity using inherent characteristics, registered information, and organizational context, shifting from “what the device claims it is” to “what evidence proves it is.”
It means building a high-confidence identity record for each device using hard-to-fake characteristics plus context such as where the device is connected, what role it serves, and whether it belongs there.
This layer continuously checks whether a device is allowed to operate in its current state by validating behavior, configuration, location, role, and policy alignment over time.
Posture refers to the living condition of an asset, including how it is configured, how it behaves, and whether it continues to align with defined policy and expected function.
Because it helps teams understand what must be remediated first, where enforcement should be immediate, and what can move through workflow or review.
This is the action layer, where organizations can notify, alert, quarantine, restrict, deny, or trigger automated remediation for unauthorized or non-compliant devices in real time.
Enforcement must be based on verified identity, posture, and risk, not on assumptions or spoofable indicators.
The framework operates as a continuous loop: visibility ensures nothing is missed, identification establishes trusted identity, posture checks compliance, risk prioritizes action, and enforcement reduces exposure.
Risk scoring is based on evidence from visibility, identity, and posture, combined with business impact. The white paper says effective scoring should consider likelihood, impact, confidence, and urgency.
The intended outcome is stronger Zero Trust assurance at the hardware layer, reduced exposure to hidden or unauthorized devices, and more effective operational prioritization and enforcement.
Sepio positions itself as enabling Zero Trust at the hardware foundation by helping organizations verify that their network hardware and connected physical devices are trustworthy.
ZTHA is relevant across IT, OT, IoT, peripherals, and other physical assets, especially in environments where fragmented tools and unmanaged devices create blind spots.
No, organizations still need traditional security tools for tactical response, while Zero Trust and ZTHA provide the strategic framework to reduce implicit trust and identify threats earlier.
The first step is reliable, continuous visibility into what is physically connected, this is the non-negotiable foundation for every other control.