In mergers and acquisitions, buyers inherit more than revenue, operations, and customers. They also inherit cyber risk.
That matters more in 2026 than ever before. PwC’s 2026 M&A outlook says AI due diligence should be a core part of every deal, and Deloitte found that 86% of surveyed corporate and private equity leaders already use GenAI in M&A, including 35% in due diligence. Deloitte also found that data security is the top barrier to broader GenAI use in dealmaking, cited by 67% of respondents.
Traditional cyber due diligence often focuses on policies, software posture, questionnaires, and declared inventories. But those methods may miss a critical issue: whether the connected hardware environment is actually known and trustworthy.
Sepio helps organizations apply Zero Trust Hardware Access to M&A due diligence by validating connected assets based on their physical truth rather than only on declared identity.
The challenge
During an acquisition, the target environment may contain:
- rogue network-connected devices
- unmanaged USB peripherals
- spoofed or mislabeled assets
- shadow IT
- dormant implants
- legacy hardware missing from the CMDB
- third-party or remote assets outside normal inventory controls
If these assets are not discovered before close, they can become inherited exposure after close.
This risk becomes more significant during integration, when systems connect, trust boundaries expand, and previously isolated issues can affect the broader enterprise.
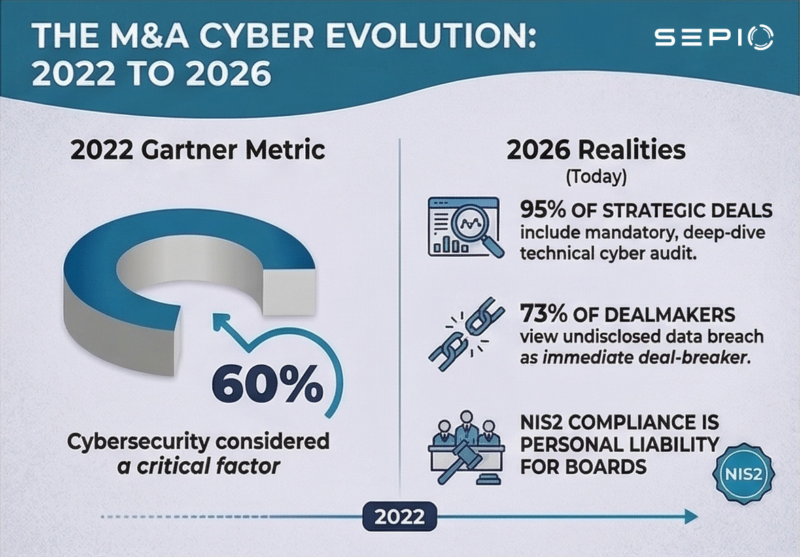
Why this use case matters now
Cybersecurity has become a strategic factor in modern dealmaking.
PwC now advises dealmakers to make AI due diligence a core part of every deal, reflecting how closely cyber posture, AI readiness, and business viability are now tied to valuation and underwriting. Deloitte’s M&A GenAI research shows that AI is already being used heavily in pre-sign stages such as strategy, target screening, and diligence, while security concerns remain the biggest obstacle to broader adoption.
At the same time, the cyber market itself reflects the strategic importance of this issue. Momentum Cyber reported 400 cybersecurity M&A deals and $96 billion in M&A deal value in 2025, within a record $119 billion in total strategic activity across acquisitions, IPOs, and financings.
For regulated industries, governance pressure is also rising. The European Commission says the NIS2 Directive establishes a unified cybersecurity framework across 18 critical sectors in the EU.
Where conventional diligence falls short
Most tools still trust what a device says it is.
They rely on declared identity, software agents, asset records, or traffic-based assumptions. In M&A scenarios, that is often not enough.
A device may appear legitimate while actually being unmanaged, unauthorized, spoofed, repurposed, or completely unknown.
That is why Zero Trust cannot be complete if hardware identity is assumed.
How Sepio helps
Sepio helps acquirers improve cyber due diligence by validating the real hardware environment.
Using physical-layer intelligence and AssetDNA, Sepio helps organizations identify connected assets based on their actual hardware characteristics across network and USB environments. This enables deeper visibility into known, unknown, unmanaged, and suspicious devices.
Before close
Sepio helps organizations:
- uncover hidden assets not reflected in standard inventories
- identify unmanaged or suspicious hardware
- improve confidence in the target’s real security posture
- support more accurate remediation and integration planning
During integration
Sepio helps organizations:
- maintain visibility beyond a one-time diligence snapshot
- detect newly introduced hardware risk
- identify unknown devices and policy violations early
- reduce the chance that inherited exposure moves silently into the combined estate
After close
Sepio helps organizations:
- strengthen Zero Trust programs with verified hardware identity
- improve risk prioritization for connected assets
- support enforcement through existing security workflows
- increase trust in the integrity of the combined infrastructure
Business value
Applying Sepio to M&A cyber due diligence can help organizations:
- reduce uncertainty before acquisition
- improve cyber risk visibility during underwriting
- support negotiation and remediation planning
- accelerate safer post-merger integration
- reduce the likelihood of inherited hidden exposure
Who this use case is for
This use case is especially relevant for:
- financial institutions
- healthcare organizations
- manufacturers
- critical infrastructure operators
- government environments
- large enterprises with complex distributed asset environments
These organizations often face higher integration complexity, stronger governance requirements, and greater exposure to hidden hardware risk during M&A.
Key takeaway
The core M&A cybersecurity challenge is not only known vulnerabilities. It is also the possibility of inheriting hidden exposure from devices and assets that were never properly identified during diligence.
Sepio helps reduce that risk by exposing the real hardware truth behind connected assets.
With Zero Trust Hardware Access, acquiring organizations can move from assumed trust to verified trust throughout the transaction lifecycle.
See what conventional M&A cyber diligence may be missing
Sepio helps organizations apply Zero Trust Hardware Access to mergers, acquisitions, and post-close integration by exposing the real hardware truth behind connected assets.
Talk to Sepio about M&A cybersecurity due diligence
Download Case Study





