Deliver automated risk mitigation at scale by translating verified device identity into policy enforcement and remediation guidance.
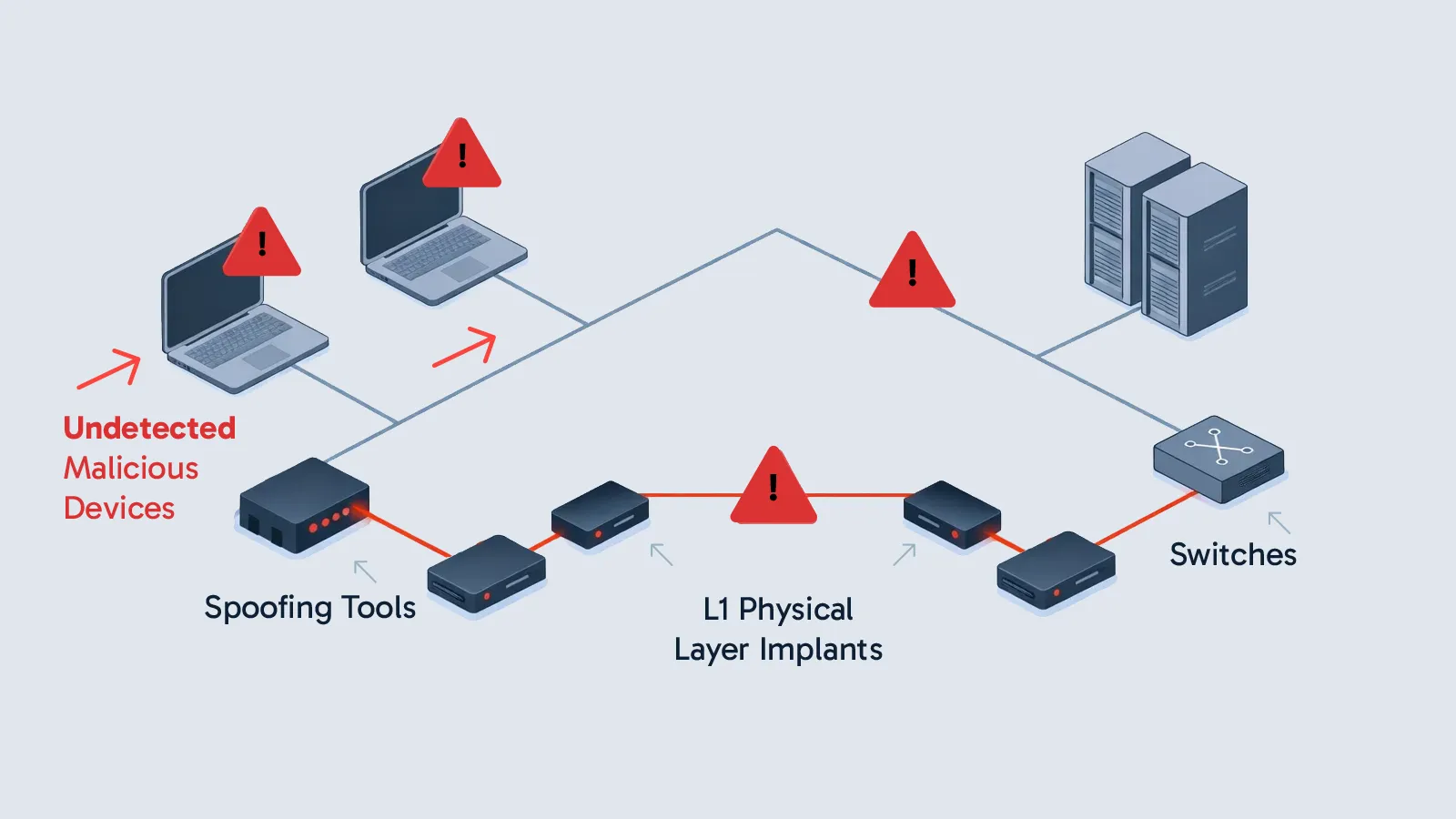
Most Zero Trust programs still start with and unsafe assumption: they trust the identity of a device based on what that device reports or what an inventory system says. This creates dangerous blind spots, especially with unmanaged, dormant, or spoofed hardware, where attackers can impersonate trusted assets and slip past traditional security controls.
When identity is uncertain, Zero Trust is then policy on paper, not protection in practice.
Key Network Security Risks:

Sepio delivers the missing foundation of Zero Trust by validating devices based on what they physically are, not what they claim to be. Using physical‑layer metadata, Sepio generates a unique Hardware AssetDNA, revealing impersonation, spoofing, and hidden risks that traditional cybersecurity tools cannot detect.
In a world where every connected device can become a potential entry point for attackers, securing the hardware layer is no longer optional. The Zero Trust Hardware Access (ZTHA) Framework provides a structured approach to identifying, validating, and enforcing trust across all physical assets—regardless of their type, behavior, or location. By shifting from implicit trust to continuous verification, this framework ensures that every device is known, authenticated, compliant, and governed by dynamic policies that reduce risk and strengthen organizational resilience.
Key Capability: Comprehensive Asset Discovery
Requirement: Discover and map all connected devices (IT, IoT, Shadow IT, USB etc.) including those invisible to network-centric tools
Key Capability: Identity Verification
Requirement: Establish asset identity based on its own characterizes, registered information and organizational context
Key Capability: Compliance Validation
Requirement: Continuous validation of the device’s behavior, configuration, and compliance against a security policy
Key Capability: Risk Assignment and Scoring
Requirement: Continuous validation of the device’s behavior, configuration, and compliance against a security policy
Key Capability: Access Control and Active Remediation
Requirement: Notify, alert and actively deny unauthorized/non-compliant devices in real-time